現在大多數企業都是使用linux作為服務器,不僅是linux是開源系統,更是因為linux比windows更安全。但是由于管理員的安全意識不全或者疏忽,導致linux的敏感端口和服務沒有正確的配置,可能會被惡意利用,所以需要進行基線加固。
1.基線 即安全基線配置,諸如操作系統、中間件和數據庫的一個整體配置,這個版本中各項配置都符合安全方面的標準。比如在系統安裝后需要按安全基線標準,將新機器中各項配置調整到一個安全、高效、合理的數值。
2.基線掃描 使用自動化工具、抓取系統和服務的配置項。將抓取到的實際值和標準值進行對比,將不符合的項顯示出來,最終以報告 的形式體現出掃描結果有的工具將配置采集和配置對比分開,通過自動化腳本采集配置后再通過特別的軟件轉換為適合人類閱讀的文檔
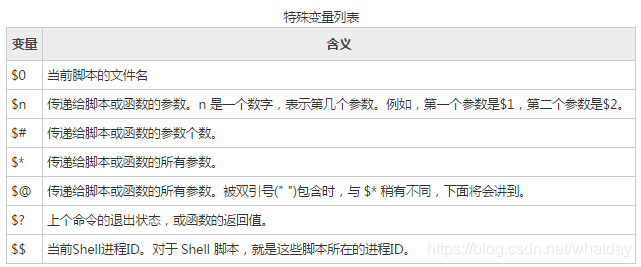
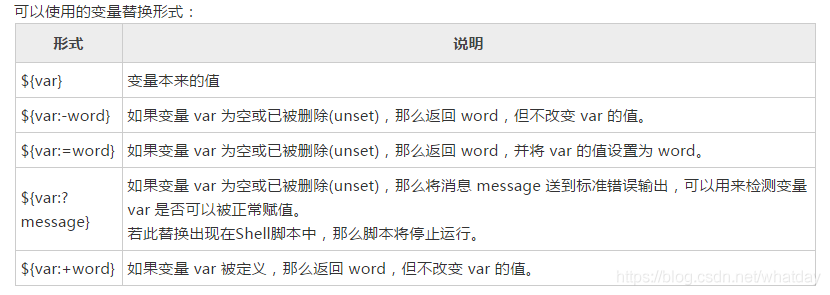
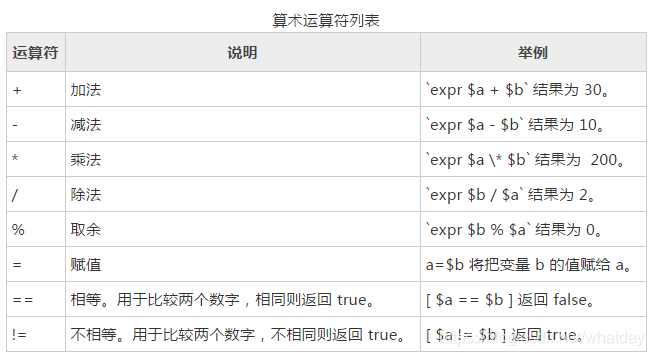
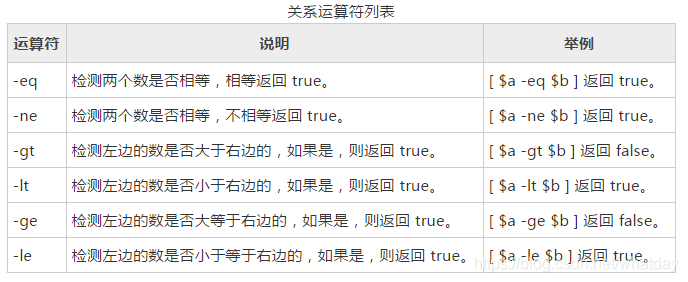
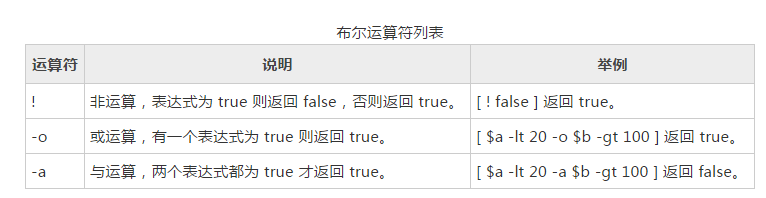
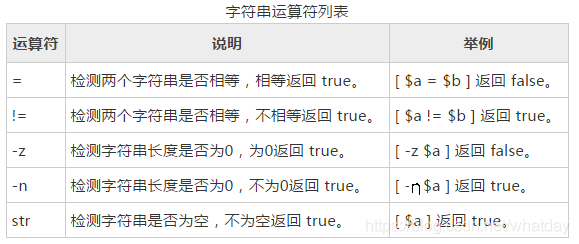
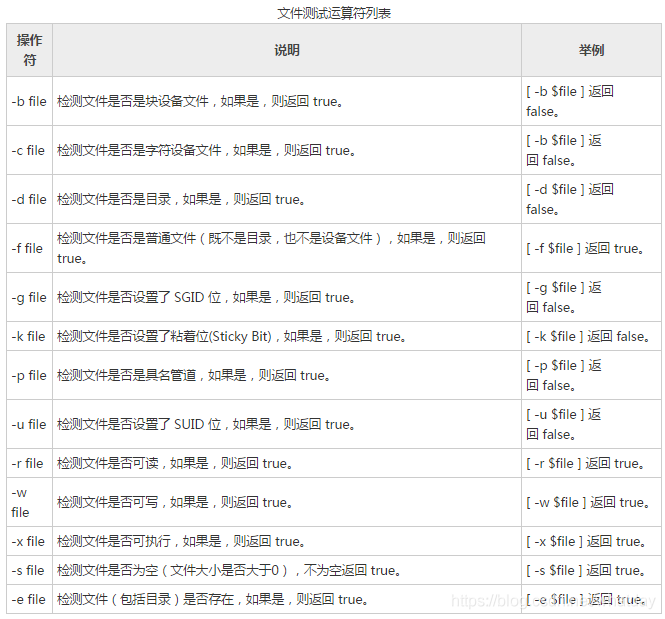
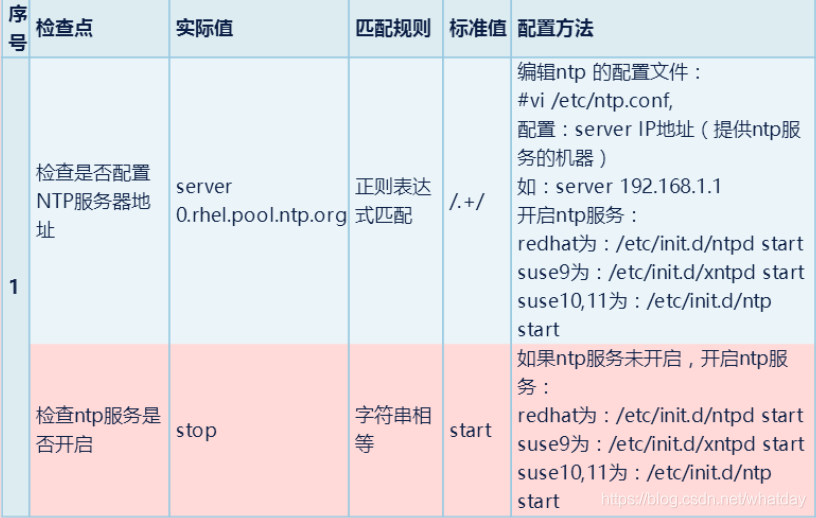
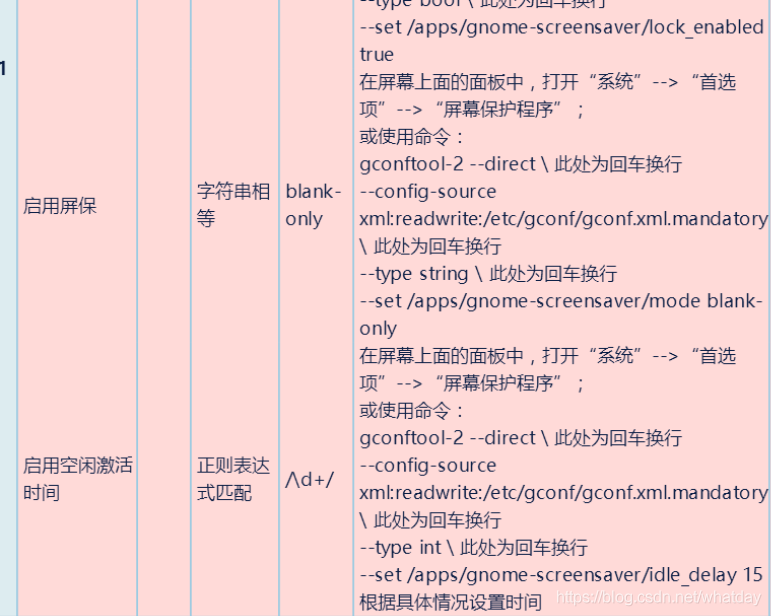
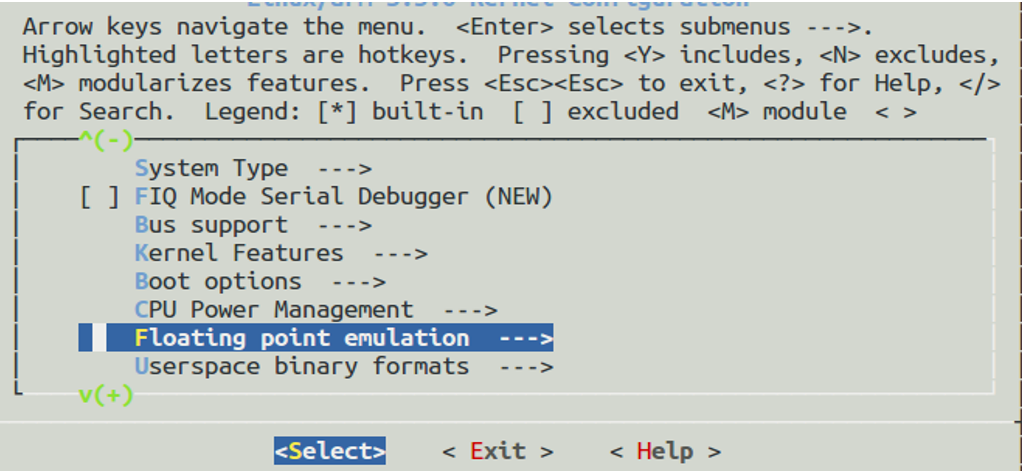
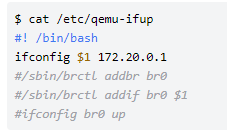
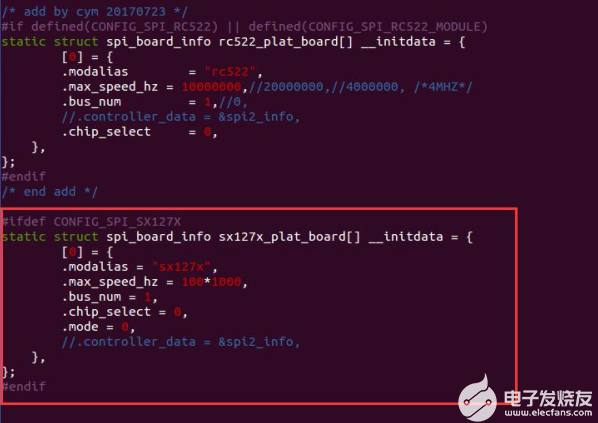
3.基線加固自動化腳本的編寫 本篇文章主要是記錄和學習安全加固腳本,首先放幾張安全加固shell腳本的命令語法:

基本命令語法介紹完了,借用網上的腳本來學習:
在執行腳本前需要提前做好備份:
#!/bin/bash cp?/etc/login.defs?/etc/login.defs.bak cp?/etc/security/limits.conf?/etc/security/limits.conf.bak cp?/etc/pam.d/su??/etc/pam.d/su.bak cp?/etc/profile?/etc/profile.bak cp?/etc/issue.net?/etc/issue.net.bak cp?/etc/shadow?/etc/shadow.bak cp?/etc/passwd?/etc/passwd.bak cp?/etc/pam.d/passwd??/etc/pam.d/passwd.bak cp?/etc/pam.d/common-password?/etc/pam.d/common-password.bak cp?/etc/host.conf?/etc/host.conf.bak cp?/etc/hosts.allow?/etc/hosts.allow.bak cp?/etc/ntp.conf?/etc/ntp.conf.bak cp?-p?/etc/sysctl.conf?/etc/sysctl.conf.bak echo?"============備份完成==================
檢查是否設置口令更改最小間隔天數
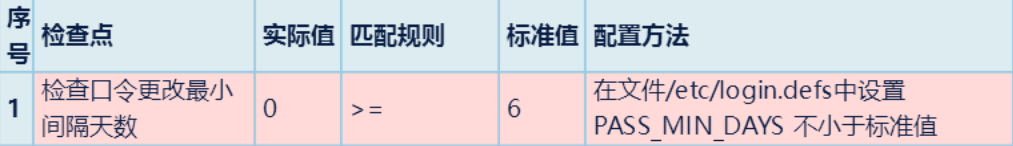
MINDAY=`cat?-n?/etc/login.defs?|?grep?-v?".*#.*"|?grep?PASS_MIN_DAYS|awk?'{print?$1}'`
sed?-i?''$MINDAY's/.*PASS_MIN_DAYS.*/PASS_MIN_DAYS?6/'?/etc/login.defs
echo?"檢查口令更改最小間隔天數完成"
2.檢查是否設置口令過期前警告天數
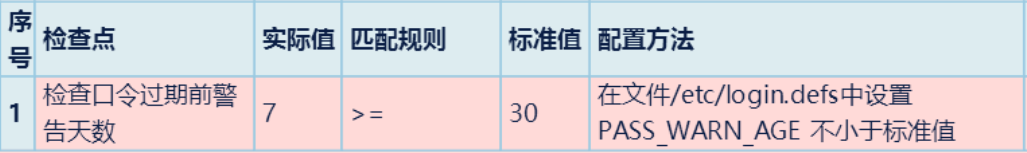
WARNAGE=`cat?-n?/etc/login.defs?|?grep?-v?".*#.*"|?grep?PASS_WARN_AGE|awk?'{print?$1}'`
sed?-i?''$WARNAGE's/.*PASS_WARN.*/PASS_WARN_AGE?30/'?/etc/login.defs
echo?"檢查口令過期前警告天數完成"
3.檢查口令生存周期
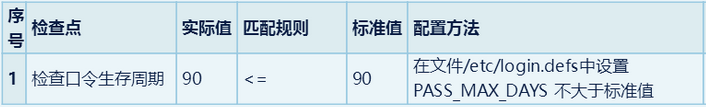
MAXDAY=`cat?-n?/etc/login.defs?|?grep?-v?".*#.*"|?grep?PASS_MAX_DAYS|awk?'{print?$1}'`
sed?-i?''$MAXDAY's/.*PASS_MAX.*/PASS_MAX_DAYS?90/'?/etc/login.defs
echo?"檢查口令生存周期完成"
4.檢查口令最小長度
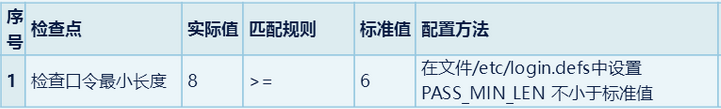
MINLEN=`cat?-n?/etc/login.defs?|?grep?-v?".*#.*"|?grep?PASS_MIN_LEN|awk?'{print?$1}'`
sed?-i?''$MINDAY's/.*PASS_MIN_LEN.*/PASS_MIN_?LEN?6/'?/etc/login.defs
echo?"檢查口令最小長度"
5.檢查是否設置grub,lilo密碼
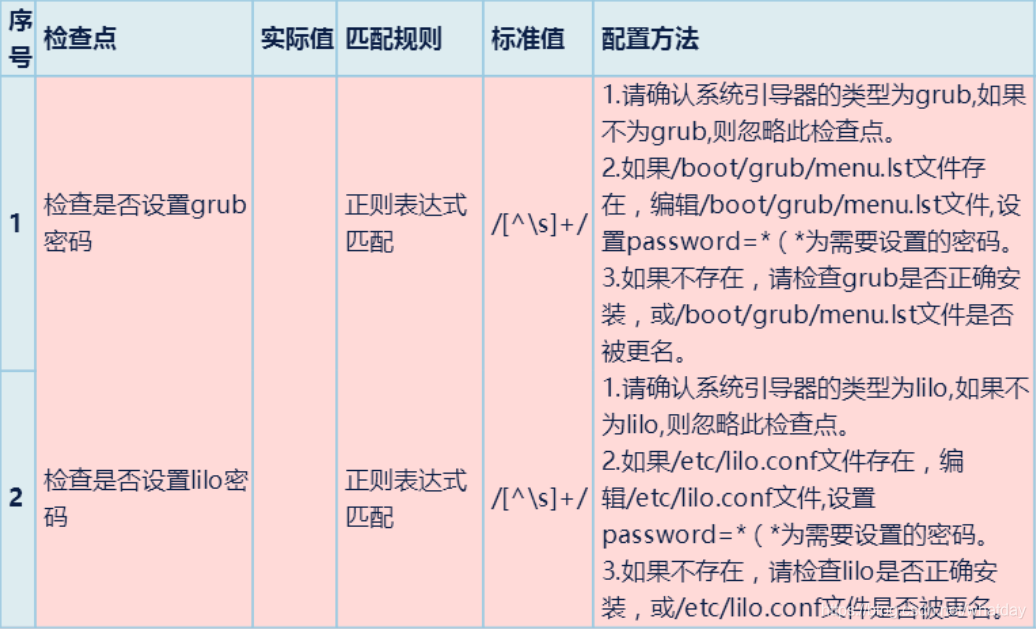
grub="/etc/menu.lst" if?[?!?-x?"$grub"?];then touch?"$grub" echo?password=123456?>>?"$grub" else? echo?password=123456?>>?"$grub" fi lilo="/etc/lilo.conf" if?[?!?-x?"$lilo"?];then touch?"$lilo" echo?password=123456?>>?"$lilo" else echo?password=123456?>>?"$lilo" fi
6.檢查是否設置core
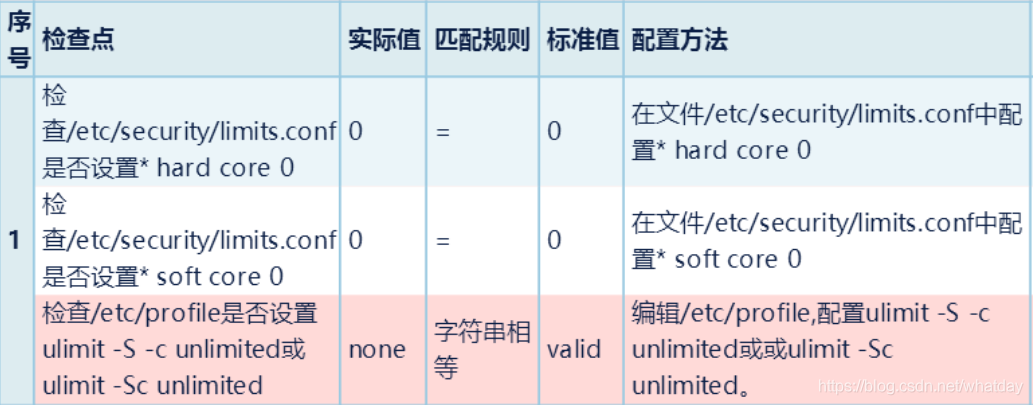
?
?
c=`cat?-n?/etc/security/limits.conf?|?grep?"#root"?|?awk?'{print?$1}'`
d=`cat?-n?/etc/security/limits.conf?|?grep?"#root"?|?awk?'{print?$5}'`
sed?-i?''$c'?s/$d/0/g'?/etc/security/limits.conf
echo?"設置*?hard?core?0完成"
e=`cat?-n?/etc/security/limits.conf?|?grep?soft?|?grep?core?|?awk?'{print?$1}'`
f=`cat?-n?/etc/security/limits.conf?|?grep?soft?|?grep?core?|?awk?'{print?$5}'`
sed?-i?''$e'?s/'$f'/0/g'?/etc/security/limits.conf
echo?"設置*?soft?core?0完成"
7.檢查系統是否禁用ctrl+alt+del組合

a=`cat?-n?/etc/control-alt-delete.conf|grep?-v?"#"?|?grep?/sbin/shutdown?|?awk?'{print?$1}'` if?[?-z?$a?];then ???echo?ok else ???sed?-i?''$a'?s/^/#/'?/etc/control-alt-delete.conf fi
8.檢查保留歷史記錄文件的大小與數量
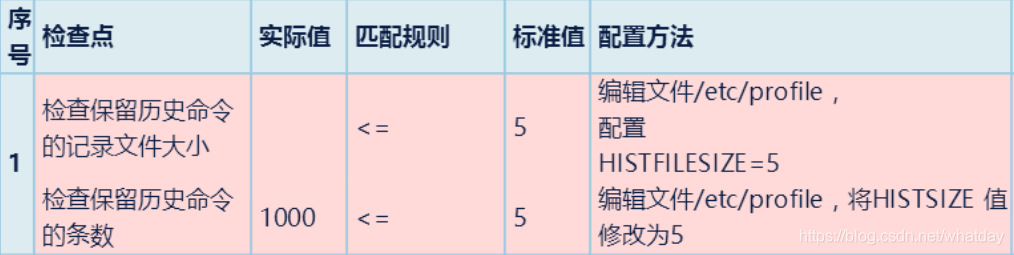
echo?"HISTFILESIZE=5"?>>?/etc/profile echo?"??檢查保留歷史命令的記錄文件大小完成" echo?"HISTSIZE=5"?>>?/etc/profile echo?"檢查保留歷史命令的條數完成"
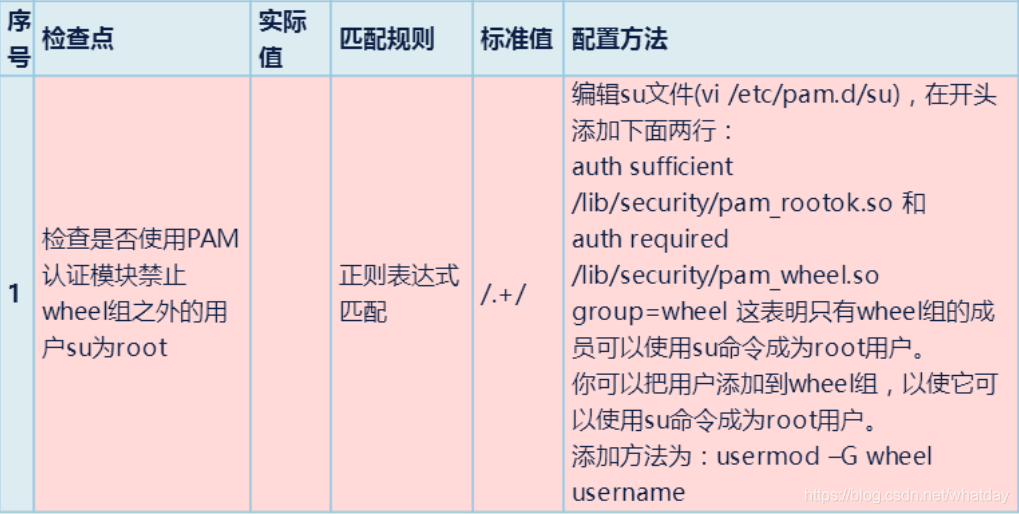
9.檢查是否使用PAM認證模塊禁止wheel組之外的用戶su為root
10.檢查是否刪除了/etc/issue.net文件
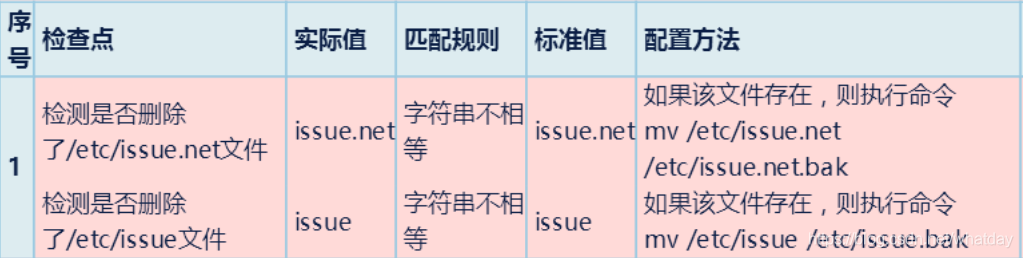
if?[?-f?/etc/issue.net?] then mv?/etc/issue.net?/etc/issue.net.bak else echo?"issue.net?文件不存在" fi if?[?-f?/etc/issue?] then mv?/etc/issue?/etc/issue.bak else echo?"issue?文件不存在" fi
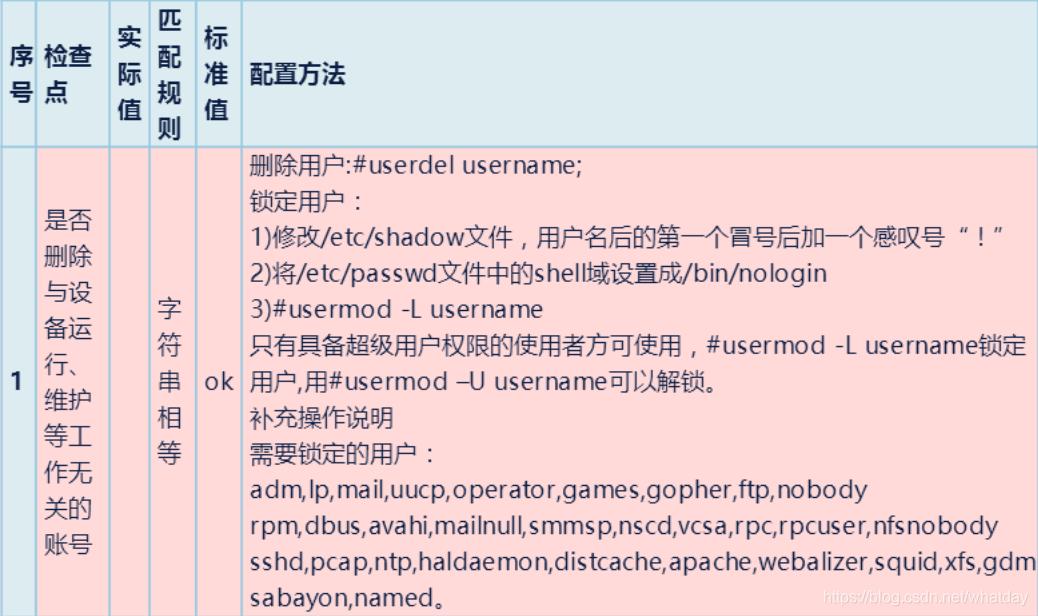
11.是否刪除與設備運行,維護等工作無關的賬戶
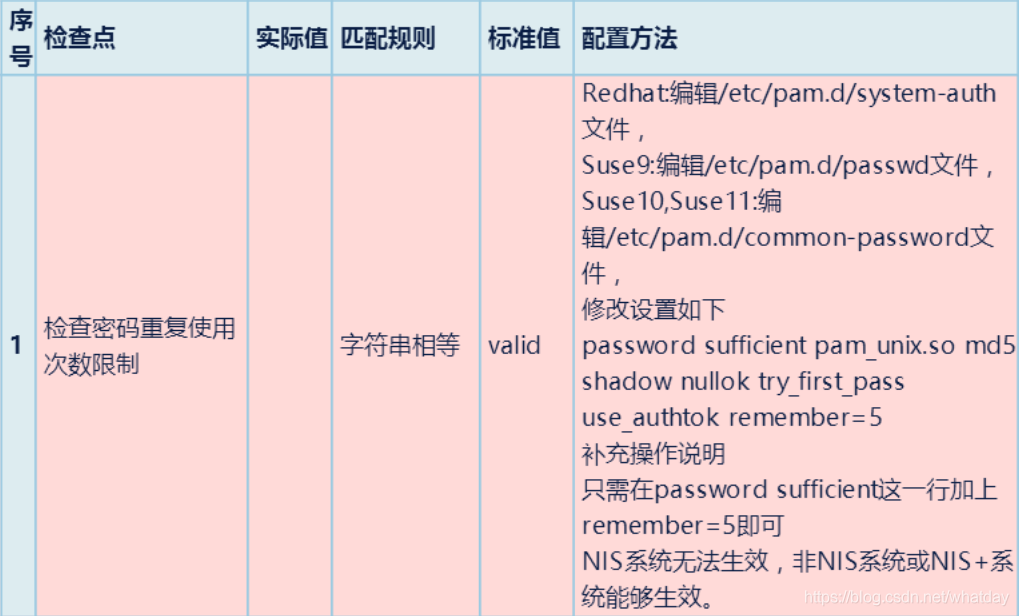
12.檢查密碼重復使用次數限制
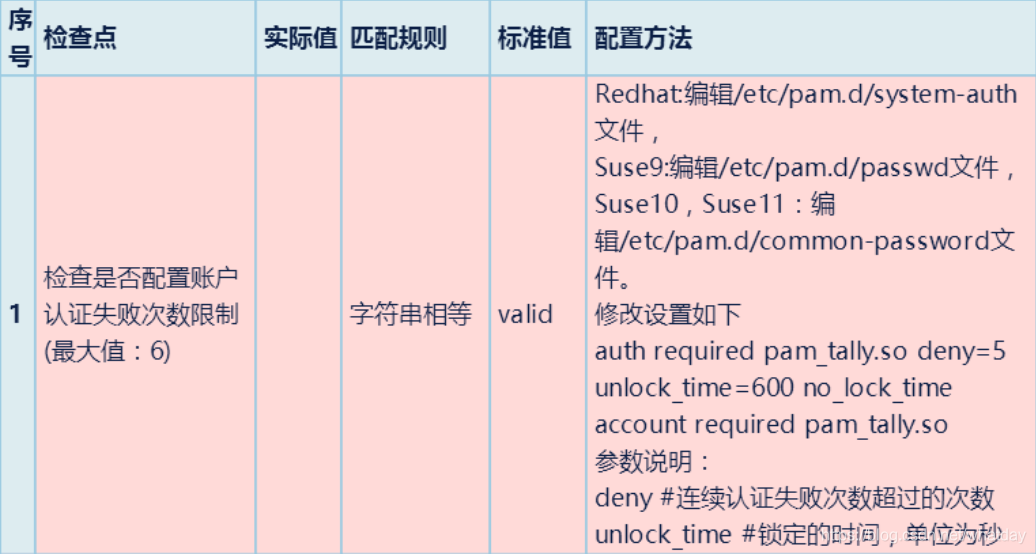
13.檢查是否配置賬戶認證失敗次數限制
cd?/etc/pam.d
if?[?-f?system-auth?];then
cp?/etc/pam.d/system-auth??/etc
#num=`grep?-n?"md5"?/etc/system-auth?|?cut?-d?":"?-f?1`
#sed?-i?''$num'????r?s/$/?remember=5'?/etc/system-auth
kk=`cat?-n?/etc/system-auth?|?grep?-v?".*#.*"|?grep?md5|awk?'{print?$1}'`
echo?$kk
version="password????sufficient????pam_unix.so?md5?shadow?nullok?try_first_pass?use_authtok?remember=500"
sed?-i?""$kk"c?$version"?/etc/system-auth
letter=`cat?-n?/etc/system-auth?|grep?password?|?grep?requisite?|?awk?'{print?$1}'`
sed?-i?''$letter's/pam_cracklib.so/&?ucredit=-1?lcredit=-1?dcredit=-1?/'?/etc/pam.d/system-auth
fi
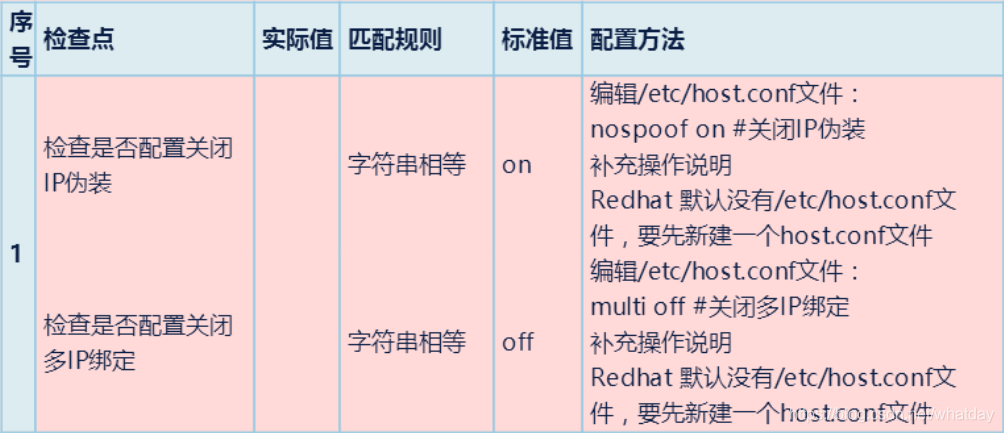
14.檢查是否配置關閉IP偽裝與綁定
snu=`cat?/etc/host.conf?|?awk?'{print?$2}'`
if?[?"$snu"?=?"on"?];?then
echo?"沒有關閉ip偽裝"
fi
sed?-i?'s/on/off/g'?/etc/host.conf
echo?"??關閉IP偽裝完成"
15.檢查/etc/hosts配置

if?[?-f?hosts.allow?];then cp?/etc/hosts.allow?/etc/ echo?"allall"?>>?/etc/hosts.allow echo?"sshdall"?>>?/etc/hosts.allow fi cd?/etc if?[?-f?hosts.deny?];then cp?/etc/hosts.deny?/etc/ echo?"all:all"?>>?/etc/hosts.deny fi
16.檢查相關服務狀態
17.檢查重要文件是否存在suid和sgid權限

find?/usr/bin/chage?/usr/bin/gpasswd?/usr/bin/wall?/usr/bin/chfn?/usr/bin/chsh?/usr/bin/newgrp?/usr/bin/write?/usr/sbin/usernetctl?/usr/sbin/traceroute?/bin/mount?/bin/umount?/bin/ping?/sbin/netreport?-type?f?-perm?+6000?2>/dev/null?>file.txt if?[?-s?file.txt?];?then echo?" find。。這條命令有輸出" for?i?in?`cat?file.txt` do chmod?755?$idoneelse echo?"find 。。這條命令沒有輸出" fi
18.其他
19.權限設置
chmod?644?/etc/passwd chmod?644?/etc/group chmod?400?/etc/shadow #chmod?600?/etc/xinetd.conf chmod?644?/etc/services chmod?600?/etc/security chmod?600?/etc/grub.conf chmod?600?/boot/grub/grub.conf chmod?600?/etc/lilo.conf echo?"文件權限設置完成"
經典綜合腳本鑒賞:
1、
echo?---------------開始--------------------
echo?---------------aboutkey----------------
cd?/etc
if?[?-f?login.defs?];then
cp?/etc/login.defs??/home/test1
MINDAY=`cat?-n?/home/test1/login.defs?|?grep?-v?".*#.*"|?grep?PASS_MIN_DAYS|awk?'{print?$1}'`
sed?-i?''$MINDAY's/.*PASS_MIN_DAYS.*/PASS_MIN_DAYS?6/'?/home/test1/login.defs
WARNAGE=`cat?-n?/home/test1/login.defs?|?grep?-v?".*#.*"|?grep?PASS_WARN_AGE|awk?'{print?$1}'`
sed?-i?''$WARNAGE's/.*PASS_WARN.*/PASS_WARN_AGE?30/'?/home/test1/login.defs
MAXDAY=`cat?-n?/home/test1/login.defs?|?grep?-v?".*#.*"|?grep?PASS_MAX_DAYS|awk?'{print?$1}'`
sed?-i?''$MAXDAY's/.*PASS_MAX.*/PASS_MAX_DAYS?90/'?/home/test1/login.defs
MINLEN=`cat?-n?/home/test1/login.defs?|?grep?-v?".*#.*"|?grep?PASS_MIN_LEN|awk?'{print?$1}'`
sed?-i?''$MINDAY's/.*PASS_MIN_LEN.*/PASS_MIN_?LEN?6/'?/home/test1/login.defs
fi
echo?--------------------ok---------------------------
echo?-------------------stop?the?del------------------------
cd?/etc/init
if?[?-f?control-alt-delete.conf?];then
cp?/etc/init/control-alt-delete.conf?/home/test1
#delete=`grep?-n?"/sbin/shutdown?-r?now"?/home/test1/control-alt-delete.conf?|?cut?-d?":"?-f?1`
#sed?-i?''$delete'?r?s/^/#/'?/home/test1/control-alt-delete.conf
#cp?/etc/init/control-alt-delete.conf?/home/test1
#num1=`grep?-n?"/sbin/shutdown"?/home/test1/control-alt-delete.conf?|?cut?-d?""?-f?1`
#sed?-i?''$num'?r?s/^/#/'?/home/test1/control-alt-delete.conf
#a=`cat?-n?/home/test1/control-alt-delete.conf|grep?-v?"#"?|?grep?"/sbin/shutdown"?|?awk?'{print?$1}'`
#text=`sed?-n?"$a"p?/home/test1/control-alt-delete.conf`
#sed?-i?''$a'c?#?'$text''?/home/test1/control-alt-delete.conf
a=`cat?-n?/home/test1/control-alt-delete.conf|grep?-v?"#"?|?grep?/sbin/shutdown?|?awk?'{print?$1}'`
????if?[?-z?$a?];then
????echo?ok
????else
????sed?-i?''$a'?s/^/#/'?/home/test1/control-alt-delete.conf
????fi
fi
echo?---------------------ok---------------------------------------
echo?------------------------grub?and?lilo?key------------------------
grub="/home/test1/menu.lst"
if?[?!?-x?"$grub"?];then
touch?"$grub"
echo?password=123456?>>?"$grub"
else?
echo?password=123456?>>?"$grub"
fi
lilo="/home/test1/lilo.conf"
if?[?!?-x?"$lilo"?];then
touch?"$lilo"
echo?password=123456?>>?"$lilo"
else
echo?password=123456?>>?"$lilo"
fi
echo?---------------------ok--------------------------------------
echo?----------------------the?history?of?mouthpasswd------------------
cd?/etc
if?[?-f?profile?];then
cp?/etc/profile?/home/test1
#num=`sed?-n?/home/test1/profile?|?grep?HISTFILESIZE?|?awk?'{print?$1}'`
?#/home/test1/profile?|?sed?$num'c?HISTFILESIZE=5'
echo?"HISTFILESIZE=5"?>>?/home/test1/profile
echo?"ulimit?-S?-c?unlimited"?>>?/home/test1/profile
fi
echo?-------------------------ok---------------------?
echo?------------------------issue-----------------
#issu="/etc/issue.net"
cd?/etc
if?[?-f?issue.net?];then
cp??issue.net??/home/test1/issue.net.bak
echo?ok
fi
echo?ok
if?[?-f?issue?];then
cp?issue?/home/test1/issue.bak
echo?ok
fi
echo?-----------------------allow/deny?ip-------------------
cd?/etc
if?[?-f?hosts.allow?];then
cp?/etc/hosts.allow?/home/test1
echo?"allall"?>>?/home/test1/hosts.allow
echo?"sshdall"?>>?/home/test1/hosts.allow
fi
cd?/etc
if?[?-f?hosts.deny?];then
cp?/etc/hosts.deny?/home/test1
echo?"all:all"?>>?/home/test1/hosts.deny
fi
echo?-----------------ok------------------------
#/etc/init.d/xinetd?restart
echo?-----------------------------core?dump-------------------
cd?/etc/security
if?[?-f?limits.conf?];then?
cp?/etc/security/limits.conf??/home/test1
echo?"*soft?core?0"?>>?/home/test1/limits.conf
echo?"*hard?core?0"?>>?/home/test1/limits.conf
fi
echo?--------------ok-------------------------
echo?----------------------------passwdrepeat---------------------
cd?/etc/pam.d
if?[?-f?system-auth?];then
cp?/etc/pam.d/system-auth??/home/test1
#num=`grep?-n?"md5"?/home/test1/system-auth?|?cut?-d?":"?-f?1`
#sed?-i?''$num'????r?s/$/?remember=5'?/home/test1/system-auth
kk=`cat?-n?/home/test1/system-auth?|?grep?-v?".*#.*"|?grep?md5|awk?'{print?$1}'`
echo?$kk
version="password????sufficient????pam_unix.so?md5?shadow?nullok?try_first_pass?use_authtok?remember=500"
sed?-i?""$kk"c?$version"?/home/test1/system-auth
letter=`cat?-n?/home/test1/system-auth?|grep?password?|?grep?requisite?|?awk?'{print?$1}'`
sed?-i?''$letter's/pam_cracklib.so/&?ucredit=-1?lcredit=-1?dcredit=-1?/'?/etc/pam.d/system-auth
fi
echo?-----------------ok--------------------
echo?--------------------超出退出--------------
cd?/etc
if?[?-f?profile?];then
cp?/etc/profile?/home/test1
echo?"export?TMOUT=600"?>>?/home/test1/profile
fi
echo?------------------ok-------------------
echo?------------------權限-------------------
chmod?644?/etc/passwd
chmod?644?/etc/group
chmod?400?/etc/shadow
#chmod?600?/etc/xinetd.conf
chmod?644?/etc/services
chmod?600?/etc/security
chmod?600?/etc/grub.conf
chmod?600?/boot/grub/grub.conf
chmod?600?/etc/lilo.conf
echo?------------------unmask--------------------
cp?/etc/csh.cshrc?/home/test1
cp?/etc/csh.login?/home/test1
cp?/etc/bashrc?/home/test1
cp?/etc/profile?/home/test1
sed?-i?'11?s/.*umask.*/umask?077/'?/home/test1/csh.cshrc
sed?-i?'58?s/.*umask.*/umask?077/'?/home/test1/csh.login
sed?-i?'66?s/.*UMASK.*/UMASK?077/'?/home/test1/bashrc
sed?-i?'62s/.*umask.*/umask?077/'?/home/test1/profile
echo?--------------------before?login?banner-------------------
cd?/etc
if?[?-f?ssh_banner?];then
touch?/etc/ssh_banner
chown?bin:bin?/etc/ssh_banner
chmod?644?/etc/ssh_banner
echo?"Authorized?only.All?activity?will?be?monitored?and?reported"?>?/etc/ssh_banner
fi
echo?-----------------------ok----------------------------
echo?-------------------stop?root?ssh?login------------------
cp?/etc/pam.d/login?/home/test1
echo?"auth???required???pam_securetty.so"?>>?/home/test1/login
cp?/etc/ssh/sshd_config?/home/test1
echo?"Banner?/etc/ssh_banner"?>>?/home/test1/sshd_config
echo?"PermitRootLogin?no"?>>?/home/test1/sshd_config
service?sshd?restart
echo?-------------------------ok-------------------
echo?--------------------openssh----------------------------
openssh=`cat?-n?/home/test1/sshd_config?|?grep?-v?".*#.*"|?grep?Protocol?|awk?'{print?$1}'`
sed?-i?''$openssh's/.*Protocol.*/Protocol?2/'?/home/test1/sshd_config
echo?-------------ok---------------------------
2、
#!/bin/bash read?key echo?"警告:本腳本只是一個檢查的操作,未對服務器做任何修改,管理員可以根據此報告進行相應的設置。" echo?---------------------------------------主機安全檢查----------------------- echo?"系統版本" uname?-a echo?-------------------------------------------------------------------------- echo?"本機的ip地址是:" ifconfig?|?grep?--color?"([0-9]{1,3}.){3}[0-9]{1,3}" echo?-------------------------------------------------------------------------- awk?-F":"?'{if($2!~/^!|^*/){print "("$1")"?"?是一個未被鎖定的賬戶,請管理員檢查是否需要鎖定它或者刪除它。"}}'?/etc/shadow echo?-------------------------------------------------------------------------- more?/etc/login.defs?|?grep?-E?"PASS_MAX_DAYS"?|?grep?-v?"#"?|awk?-F'?'??'{if($2!=90){print "/etc/login.defs里面的"$1 "設置的是"$2"天,請管理員改成90天。"}}' echo?-------------------------------------------------------------------------- more?/etc/login.defs?|?grep?-E?"PASS_MIN_LEN"?|?grep?-v?"#"?|awk?-F'?'??'{if($2!=6){print "/etc/login.defs里面的"$1 "設置的是"$2"個字符,請管理員改成6個字符。"}}' echo?-------------------------------------------------------------------------- more?/etc/login.defs?|?grep?-E?"PASS_WARN_AGE"?|?grep?-v?"#"?|awk?-F'?'??'{if($2!=10){print "/etc/login.defs里面的"$1 "設置的是"$2"天,請管理員將口令到期警告天數改成10天。"}}' echo?-------------------------------------------------------------------------- grep?TMOUT?/etc/profile?/etc/bashrc?>?/dev/null||?echo?"未設置登錄超時限制,請設置之,設置方法:在/etc/profile或者/etc/bashrc里面添加TMOUT=600參數" echo?-------------------------------------------------------------------------- if?ps?-elf?|grep?xinet?|grep?-v?"grep?xinet";then echo?"xinetd?服務正在運行,請檢查是否可以把xinnetd服務關閉" else echo?"xinetd?服務未開啟" fi echo?-------------------------------------------------------------------------- echo?"查看系統密碼文件修改時間" ls?-ltr?/etc/passwd echo?-------------------------------------------------------------------------- echo??"查看是否開啟了ssh服務" if?service?sshd?status?|?grep?-E?"listening?on|active?(running)";?then echo?"SSH服務已開啟" else echo?"SSH服務未開啟" fi echo?-------------------------------------------------------------------------- echo?"查看是否開啟了TELNET服務" if?more?/etc/xinetd.d/telnetd?2>&1|grep?-E?"disable=no";?then echo??"TELNET服務已開啟?" else echo??"TELNET服務未開啟?" fi echo?-------------------------------------------------------------------------- echo??"查看系統SSH遠程訪問設置策略(host.deny拒絕列表)" if?more?/etc/hosts.deny?|?grep?-E?"sshd:?";more?/etc/hosts.deny?|?grep?-E?"sshd";?then echo??"遠程訪問策略已設置?" else echo??"遠程訪問策略未設置?" fi echo?-------------------------------------------------------------------------- echo??"查看系統SSH遠程訪問設置策略(hosts.allow允許列表)" if?more?/etc/hosts.allow?|?grep?-E?"sshd:?";more?/etc/hosts.allow?|?grep?-E?"sshd";?then echo??"遠程訪問策略已設置?" else echo??"遠程訪問策略未設置?" fi echo?"當hosts.allow和 host.deny相沖突時,以hosts.allow設置為準。" echo?------------------------------------------------------------------------- echo?"查看shell是否設置超時鎖定策略" if?more?/etc/profile?|?grep?-E?"TIMEOUT=?";?then echo??"系統設置了超時鎖定策略?" else echo??"未設置超時鎖定策略?" fi echo?------------------------------------------------------------------------- echo?"查看syslog日志審計服務是否開啟" if?service?syslog?status?|?egrep?"?active?(running";then echo?"syslog服務已開啟" else echo?"syslog服務未開啟,建議通過service?syslog?start開啟日志審計功能" fi echo?------------------------------------------------------------------------- echo?"查看syslog日志是否開啟外發" if?more?/etc/rsyslog.conf?|?egrep?"@....|@...|@..|*.*?@....|*.*?@...|*.*?@..";then echo?"客戶端syslog日志已開啟外發" else echo?"客戶端syslog日志未開啟外發" fi echo?------------------------------------------------------------------------- echo?"查看passwd文件中有哪些特權用戶" awk?-F:?'$3==0?{print?$1}'?/etc/passwd echo?------------------------------------------------------------------------ echo?"查看系統中是否存在空口令賬戶" awk?-F:?'($2=="!!")?{print?$1}'?/etc/shadow echo?"該結果不適用于Ubuntu系統" echo?------------------------------------------------------------------------ echo?"查看系統中root用戶外連情況" lsof?-u?root?|egrep?"ESTABLISHED|SYN_SENT|LISTENING" echo?----------------------------狀態解釋------------------------------ echo?"ESTABLISHED的意思是建立連接。表示兩臺機器正在通信。" echo?"LISTENING的" echo?"SYN_SENT狀態表示請求連接" echo?------------------------------------------------------------------------ echo?"查看系統中root用戶TCP連接情況" lsof?-u?root?|egrep?"TCP" echo?------------------------------------------------------------------------ echo?"查看系統中存在哪些非系統默認用戶" echo?"root“該值大于500為新創建用戶,小于或等于500為系統初始用戶”" more?/etc/passwd?|awk?-F?":"?'{if($3>500){print "/etc/passwd里面的"$1 "的值為"$3",請管理員確認該賬戶是否正常。"}}' echo?------------------------------------------------------------------------ echo?"檢查系統守護進程" more?/etc/xinetd.d/rsync?|?grep?-v?"^#" echo?------------------------------------------------------------------------ echo?"檢查系統是否存在入侵行為" more?/var/log/secure?|grep?refused echo?------------------------------------------------------------------------ echo?"-----------------------檢查系統是否存在PHP腳本后門---------------------" if?find?/?-type?f?-name?*.php?|?xargs?egrep?-l?"mysql_query($query,?$dbconn)|專用網馬|udf.dll|class?PHPzip{|ZIP壓縮程序?荒野無燈修改版|$writabledb|AnonymousUserName|eval(|Root_CSS()|黑狼PHP木馬|eval(gzuncompress(base64_decode|if(empty($_SESSION|$shellname|$work_dir?|PHP木馬|Array("$filename"|?eval($_POST[|class?packdir|disk_total_space|wscript.shell|cmd.exe|shell.application|documents?and?settings|system32|serv-u|提權|phpspy|后門"?|sort?-n|uniq?-c?|sort?-rn?1>/dev/null?2>&1;then echo?"檢測到PHP腳本后門" find?/?-type?f?-name?*.php?|?xargs?egrep?-l?"mysql_query($query,?$dbconn)|專用網馬|udf.dll|class?PHPzip{|ZIP壓縮程序?荒野無燈修改版|$writabledb|AnonymousUserName|eval(|Root_CSS()|黑狼PHP木馬|eval(gzuncompress(base64_decode|if(empty($_SESSION|$shellname|$work_dir?|PHP木馬|Array("$filename"|?eval($_POST[|class?packdir|disk_total_space|wscript.shell|cmd.exe|shell.application|documents?and?settings|system32|serv-u|提權|phpspy|后門"?|sort?-n|uniq?-c?|sort?-rn find?/?-type?f?-name?*.php?|?xargs?egrep?-l?"mysql_query($query,?$dbconn)|專用網馬|udf.dll|class?PHPzip{|ZIP壓縮程序?荒野無燈修改版|$writabledb|AnonymousUserName|eval(|Root_CSS()|黑狼PHP木馬|eval(gzuncompress(base64_decode|if(empty($_SESSION|$shellname|$work_dir?|PHP木馬|Array("$filename"|?eval($_POST[|class?packdir|disk_total_space|wscript.shell|cmd.exe|shell.application|documents?and?settings|system32|serv-u|提權|phpspy|后門"?|sort?-n|uniq?-c?|sort?-rn?|awk?'{print?$2}'?|?xargs?-I{}?cp?{}?/tmp/ echo?"后門樣本已拷貝到/tmp/目錄" else echo?"未檢測到PHP腳本后門" fi echo?------------------------------------------------------------------------ echo?"-----------------------檢查系統是否存在JSP腳本后門---------------------" find?/?-type?f?-name?*.jsp?|?xargs?egrep?-l?"InputStreamReader(this.is)|W_SESSION_ATTRIBUTE|strFileManag|getHostAddress|wscript.shell|gethostbyname|cmd.exe|documents?and?settings|system32|serv-u|提權|jspspy|后門"?|sort?-n|uniq?-c?|sort?-rn?2>&1 find?/?-type?f?-name?*.jsp?|?xargs?egrep?-l?"InputStreamReader(this.is)|W_SESSION_ATTRIBUTE|strFileManag|getHostAddress|wscript.shell|gethostbyname|cmd.exe|documents?and?settings|system32|serv-u|提權|jspspy|后門"?|sort?-n|uniq?-c?|sort?-rn|?awk?'{print?$2}'?|?xargs?-I{}?cp?{}?/tmp/??2>&1? echo?------------------------------------------------------------------------ echo?"----------------------檢查系統是否存在HTML惡意代碼---------------------" if?find?/?-type?f?-name?*.html?|?xargs?egrep?-l?"WriteData|svchost.exe|DropPath|wsh.Run|WindowBomb|a1.createInstance|CurrentVersion|myEncString|DropFileName|a?=?prototype;|204.351.440.495.232.315.444.550.64.330"?1>/dev/null?2>&1;then echo?"發現HTML惡意代碼" find?/?-type?f?-name?*.html?|?xargs?egrep?-l?"WriteData|svchost.exe|DropPath|wsh.Run|WindowBomb|a1.createInstance|CurrentVersion|myEncString|DropFileName|a?=?prototype;|204.351.440.495.232.315.444.550.64.330"?|sort?-n|uniq?-c?|sort?-rn find?/?-type?f?-name?*.html?|?xargs?egrep?-l?"WriteData|svchost.exe|DropPath|wsh.Run|WindowBomb|a1.createInstance|CurrentVersion|myEncString|DropFileName|a?=?prototype;|204.351.440.495.232.315.444.550.64.330"?|sort?-n|uniq?-c?|sort?-rn|?awk?'{print?$2}'?|?xargs?-I{}?cp?{}?/tmp/ echo?"后門樣本已拷貝到/tmp/目錄" else echo?"未檢測到HTML惡意代碼" fi echo?"----------------------檢查系統是否存在perl惡意程序----------------------" if?find?/?-type?f?-name?*.pl?|?xargs?egrep?-l?"SHELLPASSWORD|shcmd|backdoor|setsockopt|IO::INET;"?1>/dev/null?2>&1;then echo?"發現perl惡意程序" find?/?-type?f?-name?*.pl?|?xargs?egrep?-l?"SHELLPASSWORD|shcmd|backdoor|setsockopt|IO::INET;"|sort?-n|uniq?-c?|sort?-rn find?/?-type?f?-name?*.pl?|?xargs?egrep?-l?"SHELLPASSWORD|shcmd|backdoor|setsockopt|IO::INET;"|sort?-n|uniq?-c?|sort?-rn|?awk?'{print?$2}'?|?xargs?-I{}?cp?{}?/tmp/ echo?"可疑樣本已拷貝到/tmp/目錄" else echo?"未檢測到perl惡意程序" fi echo?"----------------------檢查系統是否存在Python惡意程序----------------------" find?/?-type?f?-name?*.py?|?xargs?egrep?-l?"execCmd|cat?/etc/issue|getAppProc|exploitdb"?|sort?-n|uniq?-c?|sort?-rn find?/?-type?f?-name?*.py?|?xargs?egrep?-l?"execCmd|cat?/etc/issue|getAppProc|exploitdb"?|sort?-n|uniq?-c?|sort?-rn|?awk?'{print?$2}'?|?xargs?-I{}?cp?{}?/tmp/ echo?------------------------------------------------------------------------ echo?"-----------------------檢查系統是否存在惡意程序---------------------" find?/?-type?f?-perm?-111??|xargs?egrep?"UpdateProcessER12CUpdateGatesE6C|CmdMsg.cpp|MiniHttpHelper.cpp|y4'r3?1uCky?k1d!|execve@@GLIBC_2.0|initfini.c|ptmalloc_unlock_all2|_IO_wide_data_2|system@@GLIBC_2.0|socket@@GLIBC_2.0|gettimeofday@@GLIBC_2.0|execl@@GLIBC_2.2.5|WwW.SoQoR.NeT|2.6.17-2.6.24.1.c|Local?Root?Exploit|close@@GLIBC_2.0|syscall(\__NR\_vmsplice,|Linux?vmsplice?Local?Root?Exploit|It?looks?like?the?exploit?failed|getting?root?shell"?2>/dev/null echo?------------------------------------------------------------------------ echo?"檢查網絡連接和監聽端口" netstat?-an? echo?"--------------------------路由表、網絡連接、接口信息--------------" netstat?-rn? echo?"------------------------查看網卡詳細信息--------------------------" ifconfig?-a? echo?------------------------------------------------------------------------ echo?"查看正常情況下登錄到本機的所有用戶的歷史記錄" last echo?------------------------------------------------------------------------ echo?"檢查系統中core文件是否開啟" ulimit?-c echo?"core是unix系統的內核。當你的程序出現內存越界的時候,操作系統會中止你的進程,并將當前內存狀態倒出到core文件中,以便進一步分析,如果返回結果為0,則是關閉了此功能,系統不會生成core文件" echo?------------------------------------------------------------------------ echo?"檢查系統中關鍵文件修改時間" ls?-ltr?/bin/ls?/bin/login?/etc/passwd?/bin/ps?/usr/bin/top?/etc/shadow|awk?'{print "文件名:"$8"??""最后修改時間:"$6"?"$7}' echo?"ls文件:是存儲ls命令的功能函數,被刪除以后,就無法執行ls命令,黑客可利用篡改ls文件來執行后門或其他程序。 login文件:login是控制用戶登錄的文件,一旦被篡改或刪除,系統將無法切換用戶或登陸用戶 user/bin/passwd是一個命令,可以為用戶添加、更改密碼,但是,用戶的密碼并不保存在/etc/passwd當中,而是保存在了/etc/shadow當中 etc/passwd是一個文件,主要是保存用戶信息。 sbin/portmap是文件轉換服務,缺少該文件后,無法使用磁盤掛載、轉換類型等功能。 bin/ps 進程查看命令功能支持文件,文件損壞或被更改后,無法正常使用ps命令。 usr/bin/top top命令支持文件,是Linux下常用的性能分析工具,能夠實時顯示系統中各個進程的資源占用狀況。 etc/shadow shadow 是?/etc/passwd 的影子文件,密碼存放在該文件當中,并且只有root用戶可讀。" echo?-------------------------------------------------------------------------- echo?"-------------------查看系統日志文件是否存在--------------------" log=/var/log/syslog log2=/var/log/messages if?[?-e?"$log"?];?then echo??"syslog日志文件存在!?" else echo??"/var/log/syslog日志文件不存在!?" fi if?[?-e?"$log2"?];?then echo??"/var/log/messages日志文件存在!?" else echo??"/var/log/messages日志文件不存在!?" fi echo?-------------------------------------------------------------------------- echo?"檢查系統文件完整性2(MD5檢查)" echo?"該項會獲取部分關鍵文件的MD5值并入庫,默認保存在/etc/md5db中" echo?"如果第一次執行,則會提示md5sum:?/sbin/portmap:?沒有那個文件或目錄" echo?"第二次重復檢查時,則會對MD5DB中的MD5值進行匹配,來判斷文件是否被更改過" file="/etc/md5db" if?[?-e?"$file"?];?then?md5sum?-c?/etc/md5db?2>&1;? else? md5sum?/etc/passwd?>>/etc/md5db md5sum?/etc/shadow?>>/etc/md5db md5sum?/etc/group?>>/etc/md5db md5sum?/usr/bin/passwd?>>/etc/md5db md5sum?/sbin/portmap>>/etc/md5db md5sum?/bin/login?>>/etc/md5db md5sum?/bin/ls?>>/etc/md5db md5sum?/bin/ps?>>/etc/md5db md5sum?/usr/bin/top?>>/etc/md5db; fi echo?---------------------------------------------------------------------- echo?"------------------------主機性能檢查--------------------------------" echo?"CPU檢查" dmesg?|?grep?-i?cpu echo?----------------------------------------------------------------------- more?/proc/cpuinfo echo?----------------------------------------------------------------------- echo?"內存狀態檢查" vmstat?2?5 echo?----------------------------------------------------------------------- more?/proc/meminfo echo?----------------------------------------------------------------------- free?-m echo?----------------------------------------------------------------------- echo?"文件系統使用情況" df?-h echo?----------------------------------------------------------------------- echo?"網卡使用情況" lspci?-tv echo?---------------------------------------------------------------------- echo?"查看僵尸進程" ps?-ef?|?grep?zombie echo?---------------------------------------------------------------------- echo?"耗CPU最多的進程" ps?auxf?|sort?-nr?-k?3?|head?-5 echo?---------------------------------------------------------------------- echo?"耗內存最多的進程" ps?auxf?|sort?-nr?-k?4?|head?-5
編輯:黃飛
?
?
 電子發燒友App
電子發燒友App



















評論